openSUSE
 news.opensuse.org
news.opensuse.org
Welcome to the monthly update for Tumbleweed for September 2024! This month, the rolling-release model has kept pace with numerous important updates and bug fixes. PostgreSQL received a major update moving to 17 and text shaping engine [harfbuzz](https://github.com/harfbuzz/harfbuzz) had a major update to version 10. Packages like [systemd](https://freedesktop.org/wiki/Software/systemd/), [git](https://github.com/git), [bash](https://www.gnu.org/software/bash/) and [qemu](https://www.qemu.org/) were also updated this month in the rolling release. Various packages saw CVE fixes and desktop components for [GNOME](https://www.gnome.org/) and [KDE](https://www.kde.org/) were also updated. As always, remember to roll back using [snapper](https://github.com/openSUSE/snapper) if any issues arise. Happy updating and tumble on! Should readers desire more frequent information about snapshot updates, they are encouraged to subscribe to the [openSUSE Factory mailing list](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). ### New Features and Enhancements * [Linux Kernel](https://www.kernel.org/) 6.11.0: The latest update brings reversion of the PCI ACS configurability extension to address an issue [bsc#1229019](https://bugzilla.opensuse.org/show_bug.cgi?id=1229019). Key updates in the release include a fix to the block subsystem, resolving how the scheduler is handled in `elv_iosched_local_module`. A correction was made in the [AMD](https://www.amd.com) GPU display driver to address a mistake from a previous revert related to [bsc#1228093](https://bugzilla.opensuse.org/show_bug.cgi?id=1228093). Updates also include refreshed [ALSA](https://en.wikipedia.org/wiki/Advanced_Linux_Sound_Architecture) patches to enhance power management blacklist options. The improvements are expected to provide greater stability and performance for various hardware configurations. * [postgresql17](https://www.postgresql.org/): This major release provides key improvements like a revamped memory management system for vacuum, boosting efficiency by reducing memory usage by up to 20x along with optimized processing for high concurrency workloads. Version 17 also enhances query execution with faster processing using B-tree indexes and parallel BRIN index builds. Developers benefit from the addition of the SQL/JSON `JSON_TABLE` command and expanded MERGE capabilities, as well as a 2x speed improvement in data exports with the `COPY` command. Logical replication now simplifies major version upgrades by eliminating the need to drop replication slots, improving ease of use in high availability setups. The software package further enhances database security and operational management, with new TLS options, incremental backups, and detailed monitoring tools. * [harfbuzz](https://github.com/harfbuzz/harfbuzz) 10.0.1: Significant fixes were made for the text shaping engine including support for Unicode 16.0.0. The version has a new [Application Programming Interfaces](https://en.wikipedia.org/wiki/API) that allows clients to customize glyphs when a Unicode Variation Selector isn't supported by the font, as well as a callback for getting table tags from `hb_face_t`. Updates also address pair positioning lookup subtable application for compatibility and ensure subsetting fails if no glyphs are present to prevent silent errors. * [GNOME](https://www.gnome.org/) 46.5: [gnome-shell](https://gitlab.gnome.org/GNOME/gnome-shell) now addresses issues with smartcard logins, fixes glitches when quick settings menu animations are interrupted, and resolves problems with new Wi-Fi connections for restricted users. It also ensures required animations remain enabled, fixes display of pending PAM messages on the login screen and plugs memory leaks. Un update of the [gnome-software](https://gitlab.gnome.org/GNOME/gnome-software) has a reduction in power usage when the main window is closed, along with translation updates.. * [KDE Plasma 6.1.5](https://kde.org/announcements/plasma/6/6.1.5/): In [Discover](https://invent.kde.org/plasma/discover), snapType mapping is corrected, and [Flatpak](https://flatpak.org/) now properly reports extensions without errors. [KWin](https://userbase.kde.org/KWin) addresses several crash scenarios, such as null dereference and input event handling from removed devices. [Plasma Desktop](https://kde.org/plasma-desktop/) includes fixes for keyboard navigation in Kickoff, task list alignment in RTL mode and it has proper handling of background icons and test windows. Plasma Workspace enhances touchscreen interaction, system tray tooltips and clipboard functionality. Additional fixes included targeted crashes in hotplugging and svg rendering, while SDDM KCM improves state management. * [Frameworks 6.6.0](https://kde.org/announcements/frameworks/6/6.6.0/): [Attica](https://api.kde.org/frameworks/attica/html/index.html) adds CI jobs for Alpine/musl, while [Baloo](https://community.kde.org/Baloo) sets up crash handling for baloo_file. New icons are introduced in [Breeze](https://github.com/KDE/breeze). KCoreAddons improves [dbus](https://www.freedesktop.org/wiki/Software/dbus/) error handling and licensing, and KDeclarative adjusts rendering for better DPI positioning. [KIO](https://api.kde.org/frameworks/kio/html/index.html) resolves issues with restoring trash entries and enhances service menu handling. [KTextEditor](https://api.kde.org/frameworks/ktexteditor/html/) receives performance optimizations and additional C++ porting for sorting and unique functionalities. [Kirigami](https://kde.org/products/kirigami/) continues to improve icon handling and toolbars, while [KNewStuff](https://api.kde.org/frameworks/knewstuff/html/index.html) and [KWallet](https://github.com/KDE/kwallet)f ocus on making shared actions more reliable and enhancing crash handling. * [KDE Gear 24.08.1](https://kde.org/announcements/gear/24.08.1/): [Akademy 2024 Videos](https://tube.kockatoo.org/w/p/rHZEAD3pY3hNMTdZMLj4JJ) are out, but a lot of efforts went into last month’s conference. [Akonadi resolves](https://invent.kde.org/pim/akonadi) a crash related to query cache eviction and fixes configuration file handling. [Dolphin](https://apps.kde.org/dolphin/) improves usability with fixes for button functionality and file list resizing, while [Elisa](https://apps.kde.org/elisa/) enhances its Now Playing view and toolbar layout. [Itinerary](https://apps.kde.org/itinerary/) and [Kalarm](https://apps.kde.org/de/kalarm/) both receive updates for better dark mode handling and audio alarm functionality. [Kdenlive](https://kdenlive.org/en/) addresses multiple timeline and rendering issues, optimized keyframe handling and fixes several bugs related to effects and transitions. [Kate](https://kate-editor.org/) adds support for the [Odin](https://odin-lang.org/) language in its formatter and [Okular](https://okular.kde.org/) now sets tooltips for forms. ### Key Package Updates * [git](https://github.com/git) 2.46.1: A clarification has been made to `git checkout --ours` to inform users they need to specify paths, avoiding confusion. An issue with `git add -p` failing for users with `diff.suppressBlankEmpty` was corrected. Additionally, `git notes add -m '' --allow-empty` no longer improperly invokes an editor, and unnecessary re-encoding operations for tracing have been removed. * [qemu](https://www.qemu.org/) 9.1.0: The update introduces new migration capabilities, such as compression offload support via Intel In-Memory Analytics Accelerator (IAA) or User Space Accelerator Development Kit (UADK) and improved postcopy failure recovery. RISC-V architecture also sees support for several extensions, while x86 adds KVM support for [AMD](https://www.amd.com) SEV-SNP guests and emulation for newer Intel CPU models like Ice Llake and Sapphire Rapids. * [systemd](https://freedesktop.org/wiki/Software/systemd/) 256.6: This version no longer attempts to restart udev socket units, addressing issue [bsc#1228809](https://bugzilla.opensuse.org/show_bug.cgi?id=1228809) where safely restarting socket-activated services and their socket units simultaneously was problematic. * [pipewire](https://pipewire.org/) 1.2.4: The update addresses a crash during the cleanup of globals and enhances the `RequestProcess` dispatch mechanism. The Simple Plugin API framework now uses `systemd-logind` to detect new devices. Pulse-Code Modulation device handling is also improved. * [GStreamer](https://gstreamer.freedesktop.org/) 1.24.8: The multimedia framework package improves handling in `decodebin3` and `encodebin` for better media decoding and smart rendering, respectively. Enhancements for proper viewport resizing when video size changes were made and audio stream enhancements were made for better compatibility with Firefox. There were some stability fixes for wayland including crash prevention and [Application Binary Interface](https://en.wikipedia.org/wiki/Application_binary_interface) corrections. * [Mesa](https://www.mesa3d.org/) 24.1.7: This release continues to support [OpenGL](https://www.opengl.org//) 4.6 and [Vulkan](https://www.vulkan.org/) 1.3, though the version reported depends on the specific driver used. Key bug fixes include resolving issues with smartcard logins, race conditions when generating enums, and artifacts in games such as [Black Myth Wukong](https://store.steampowered.com/app/2358720/Black_Myth_Wukong/) and DCS World with certain GPUs. * [GTK4](https://www.gtk.org/) 4.16.1: This GTK Scene Graph Kit layer sees speed optimizations for Vulkan operations, reduces startup time by skipping unnecessary GL and Vulkan initialization and fixes a crash related to certain Vulkan drivers. Memory format conversions in [GIMP](https://www.gimp.org/) Drawing Kit are now faster. The builder-tool has also been improved for better box conversion. * [bash](https://www.gnu.org/software/bash/) 5.2.37: This update has key patches to address issues such as an incorrect handling of quoted text during auto-completion and multibyte character handling in `readline`. The update resolves system compatibility with `select` and `pselect` availability and fixes a parsing issue in compound assignments during alias expansion. A typo in the autoconf test affecting `strtold` availability when compiled with [GNU Compiler Collection](https://gcc.gnu.org/) 14 was corrected. * [vim](https://www.vim.org/) 9.1.0718: One notable fix in the text editor resolves issues with personal Vim runtime directory recognition. The update also addresses unnecessary `NULL` checks in `parse_command_modifiers()` and corrects color name parsing errors introduced in a previous version. Other improvements include updates to syntax highlighting for various file types such as HCL, Terraform, and tmux. Performance improvements were also made to include the more efficient inserting with a count and resolving cursor position crashes. ### Bug Fixes * [curl](https://curl.se/) 8.10.0: * [CVE-2024-8096](https://www.suse.com/security/cve/CVE-2024-8096.html) may have incorrectly validated certificates using Online Certificate Status Protocol stapling, ignoring certain errors like 'unauthorized'. * [OpenSSL](https://www.openssl.org/): * [CVE-2024-41996](https://www.suse.com/security/cve/CVE-2024-41996.html) was fixed, which could have allowed remote attackers to trigger costly server-side DHE calculations via public key order validation in [Diffie-Hellman](https://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange). * [postgresql17](https://www.postgresql.org/) * [CVE-2024-7348](https://www.suse.com/security/cve/CVE-2024-7348.html) fixes a race condition that could allow attackers to execute arbitrary SQL as the user running `pg_dump`. * [python311](https://www.python.org/): This package fixed a few CVE’s. Here are a couple of fixes * [CVE-2024-4030](https://www.suse.com/security/cve/CVE-2024-4030.html) had a fix to ensure Unix "700" permissions are applied to secure the directory. * [tiff](http://www.simplesystems.org/libtiff/) 4.7.0: * [CVE-2023-52356](https://www.suse.com/security/cve/CVE-2023-52356.html) had a segmentation fault allowing remote attackers to trigger a heap-buffer overflow that could cause a denial of service. * [CVE-2024-7006](https://www.suse.com/security/cve/CVE-2024-7006.html) had a null pointer dereference in that could trigger application crashes and cause denial of service. * [LibreOffice](https://www.libreoffice.org/) 24.8.1.2 * [CVE-2024-5261](https://www.suse.com/security/cve/CVE-2024-5261.html) was fixed that disabled TLS certificate verification, allowing improper certificate validation during document processing in third-party components. * [Mozilla Firefox](https://www.mozilla.org) 130.0.1: * This release fixes several CVEs. One of the most critical fixes involves [CVE-2024-8385](https://www.mozilla.org/en-US/security/advisories/mfsa2024-39/), where a WASM type confusion issue could lead to exploitable vulnerabilities. Another significant fix is for [CVE-2024-8381](https://www.mozilla.org/en-US/security/advisories/mfsa2024-39/), which could trigger a type confusion vulnerability when looking up property names within a "with" block. [CVE-2024-8388](https://www.mozilla.org/en-US/security/advisories/mfsa2024-39/) fixed an issue where fullscreen notifications could be hidden on Android devices, potentially leading to UI spoofing attacks. Two memory safety bugs, [CVE-2024-8387](https://www.mozilla.org/en-US/security/advisories/mfsa2024-39/) and [CVE-2024-8389](https://www.mozilla.org/en-US/security/advisories/mfsa2024-39/), were also patched. * [apr](https://apr.apache.org/download.cgi) 1.7.5: * [CVE-2023-49582](https://www.suse.com/security/cve/CVE-2023-49582.html) had shared memory permissions that could expose sensitive data to local users. ### Conclusion September 2024 brings important updates for Tumbleweed users. Security fixes across packages like PostgreSQL, libtiff, and LibreOffice ensure stability and security. Significant improvements were made in tools like systemd, git, and qemu, enhancing performance and compatibility. Noteworthy updates in PostgreSQL 17 and Harfbuzz 10 also bring major enhancements, contributing to a more robust and refined rolling release environment. Stay updated with the latest snapshots by subscribing to the openSUSE Factory mailing list. For those Tumbleweed users who want to contribute or want to engage with detailed technological discussions, subscribe to the [openSUSE Factory mailing list ](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). The openSUSE team encourages users to continue participating through bug reports, feature suggestions and discussions. ### Contributing to openSUSE Tumbleweed Your contributions and feedback make openSUSE Tumbleweed better with every update. Whether reporting bugs, suggesting features, or participating in community discussions, your involvement is highly valued.
cross-posted from: https://lemmy.world/post/20242590
 news.opensuse.org
news.opensuse.org
This is a quick start guide for Full Disk Encryption with TPM or FIDO2 and YaST2 on openSUSE Tumbleweed. It focuses on the few steps to install openSUSE Tumbleweed with YaST2 and using Full Disk Encryption secured by a TPM2 chip and [measured boot](https://en.opensuse.org/Portal:MicroOS/RemoteAttestation#Measured_boot) or a FIDO2 key. ## Hardware Requirement: - UEFI Firmware - TPM2 Chip or FIDO2 key which supports the hmac-secret extension - 2GB Memory ## Installation of openSUSE MicroOS There is an own [Quickstart for openSUSE MicroOS](https://microos.opensuse.org/blog/2024-09-03-quickstart-fde-yast2/) ## Installation of openSUSE Tumbleweed ### Boot installation media * Follow the workflow until "Suggested Partitioning": * Partitioning: Select "Guided Setup" and "Enable Disk Encryption", keep the other defaults * Continue Installation until "Installation Settings": * Booting: * Change Boot Loader Type from "GRUB2 for EFI" to "Systemd Boot", ignore "Systemd-boot support is work in progress" and continue * Software: * Install additional tmp2.0-tools, tpm2-0-tss and libtss2-tcti-device0 * Finish Installation ### Finish FDE Setup Boot new system * Enter passphrase to unlock disk during boot * Login * Enroll system: * With TPM2 chip: `sdbootutil enroll --method tpm2` * With FIDO2 key: `sdbootutil enroll --method fido2` * Optional, but recommended: * Upgrade your LUKS key derivation function (do that for every encrypted device listed in `/etc/crypttab`): ``` # cryptsetup luksConvertKey /dev/vdaX --pbkdf argon2id # cryptsetup luksConvertKey /dev/vdaY --pbkdf argon2id ``` ## Adjusting kernel boot parameters The configuration file for kernel command line options is `/etc/kernel/cmdline`. After editing this file, call `sdbootutil update-all-entries` to update the bootloader configuration. If that option does not exist yet or does not work, a workaround is: `sdbootutil remove-all-kernels && sdbootutil add-all-kernels`. ## Re-enrollment If the prediction system fails, a new policy must be created for the new measurements to replace the policy stored in the TPM2. If you have a recovery PIN: ``` # sdbootutil --ask-pin update-predictions ``` If you don't have the recovery PIN, you can set one with this steps: ``` # sdbootutil unenroll --method=tpm2 # PIN=<new recovery PIN> sdbootutil enroll --method=tpm2 ``` ## Virtual Machines If your machine is a VM, it is recommended to remove the "0" from the `FDE_SEAL_PCR_LIST` variable in `/etc/sysconfig/fde-tools`. An update of the hypervisor can change PCR0. Since such an update is not visible inside the VM, the PCR values cannot be updated. As result, the disk cannot be decrypted automatically at the next boot, the recovery key needs to be entered and a manual re-enrollment is necessary. ## Next Steps The next steps will be: * Support grub2-BLS (grub2 following the [Boot Loader Specification](https://uapi-group.org/specifications/specs/boot_loader_specification/)) * Add support to the installers (YaST2 and Agama) * Make this the default if a TPM2 chip is present Any help is welcome! ## Further Documentation * [Full Disk Encryption (FDE)](https://en.opensuse.org/Portal:MicroOS/FDE) * [Systemd-fde](https://en.opensuse.org/Systemd-fde) * [Systemd-boot and Full Disk Encryption with TPM and FIDO2](https://microos.opensuse.org/blog/2023-12-20-sdboot-fde/)
 lists.opensuse.org
lists.opensuse.org
The "security" development project is switched to a 4096bit RSA key. New key fingerprint: `Type : GPG public key` `User ID : security OBS Project <security@build.opensuse.org>` `Algorithm : rsa` `Key size : 4096` `Expires : 2026-12-02 13:27:55` `Fingerprint : f9fa 0223 b56b 116c 3637 37ef 5da5 7bdd 6dd7 85ca`
 news.opensuse.org
news.opensuse.org
Python 3.13 RC2 is now available in [Tumbleweed](https://get.opensuse.org/tumbleweed/). This new version of the [Python](https://www.python.org/) interpreter will be released in October 2024. There is [a lot of changes](https://www.python.org/downloads/release/python-3130rc2/) and new features in 3.13, but we're also bringing exiting experimental features in Tumbleweed. ### Experimental JIT compiler The default (`python313`) build has the flag `--enable-experimental-jit=yes-off`. This means that if you want to use this [experimental JIT](https://docs.python.org/3.13/whatsnew/3.13.html#an-experimental-just-in-time-jit-compiler) you can enable with an environment variable: ``` $ PYTHON_JIT=1 python3.13 ``` You can find more information about the JIT compiler and how it can improve performance in [PEP-744](https://peps.python.org/pep-0744/). ### Free threaded CPython (no GIL) With this new version of Python interpreter, there is an option to build without the famous [Global Interpreter Lock](https://docs.python.org/3.13/whatsnew/3.13.html#free-threaded-cpython), aka GIL. This is a really experimental feature, but why not have this on Tumbleweed? So we decided to build also this new version with a new package `python313-nogil`. This new package is an isolated interpreter, so you can install without conflicts with `python313`. The package is building with the `--disable-gil` option and it provides the `/usr/bin/python3.13t` binary. It uses by default `/usr/lib/python3.13t/site-packages` for third-party libs so, with the default configuration, it won't use any python 3.13 module. This means that now you can use `threading.Thread` in the Python interpreter, and it will be actual threads so, at the end using threads with `python3.13t`, interpreter should be a lot faster. There's no packages for this interpreter in Tumbleweed, at this moment. So if you want to use third party libraries you should use `virtualenv` and `pip` for that: ``` $ python3.13t -m venv free-threaded-env $ source free-threaded-env/bin/activate (free-threaded-env) $ pip install requests (free-threaded-env) $ python3 Python 3.13.0rc2 experimental free-threading build (main, Sep 07 2024, 16:06:06) [GCC] on linux Type "help", "copyright", "credits" or "license" for more information. >>> import sys; sys._is_gil_enabled() False ```
 news.opensuse.org
news.opensuse.org
cross-posted from: https://lemmy.ml/post/19629878 > >In recent testing scenarios involving a build and NetworkManager, a significant issue has surfaced: the network stack becomes non-operational. > > > >Users are advised to postpone system updates for now, but if users have already updated, use Snapper to rollback; it’s important to note that while the issue primarily affects GNOME setups with Wicked, it can also impact servers without these components. > > > >This problem has been consistently reproducible since at least the 20240825 Tumbleweed build. Bind 9.20.1 received an update has changes to DNS query handling and system controls, which may have inadvertently contributed to the network stack issue.
The first packages of the new COSMIC desktop has landed in openSUSE. List of packages: * [https://download.opensuse.org/tumbleweed/repo/oss/x86\_64/?P=\*cosmic](https://download.opensuse.org/tumbleweed/repo/oss/x86_64/?P=*cosmic)\* Development branch of COSMIC (stable) * [https://build.opensuse.org/project/show/X11:COSMIC:Factory](https://build.opensuse.org/project/show/X11:COSMIC:Factory) ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
 news.opensuse.org
news.opensuse.org
Welcome to the monthly update for openSUSE Tumbleweed for July 2024. Last month was busy with events like the [Community Summit in Berlin](https://events.opensuse.org/conferences/CSBerlin) and the [openSUSE Conference](https://events.opensuse.org/conferences/oSC24). Both events were productive and well-received. Despite the busy schedule and follow on discussion from the conference about the [Rebranding of the Project](https://lists.opensuse.org/archives/list/project@lists.opensuse.org/thread/E3EQOFD5NVWTM4MHLNA5MT5BGWQLUZ5U/), a number of snapshots continued to roll out to users this month. Stay tuned and tumble on! Should readers desire more frequent information about snapshot updates, they are encouraged to subscribe to the [openSUSE Factory mailing list](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). ### New Features and Enhancements ### * [Linux Kernel](https://www.kernel.org/) 6.9.9: This kernel introduces several important fixes and enhancements across various subsystems. Key updates include the introduction of `devm_mutex_init()` for mutex initialization in multiple components, addressing issues in the [Hisilicon](https://www.hisilicon.com) debugfs uninit process, and resolving shared IRQ handling in DRM Lima drivers. Fixes in the PowerPC architecture avoid `nmi_enter/nmi_exit` in real mode interrupts, while networking improvements prevent unnecessary `BUG()` calls in `net/dql`. Enhancements in WiFi drivers such as RTW89 include improved handling for 6 GHz channels. Updates in DRM/AMD drivers address multiple issues, from uninitialized variable warnings to ensuring proper timestamp initialization and memory management. The [RISC-V](https://riscv.org/) architecture receives a fix for initial sample period values, and several BPF selftests see adjustments for better error detection. These updates collectively enhance system stability, performance, and security. * [KDE Plasma 6.1.3](https://kde.org/announcements/plasma/6/6.1.3/): [Discover](https://invent.kde.org/plasma/discover) now auto-handles [Flatpak](https://flatpak.org/) rebases from runtimes and properly uninstalls EOL refs without replacements. In [Kglobalacceld](https://github.com/KDE/kglobalacceld), invalid keycodes are explicitly processed. Kpipewire introduces proper cleanup on deactivate and fixes thread handling for PipeWireSourceStream. [KScreen](https://github.com/KDE/kscreen) now uses ContextualHelpButton from [Kirigami](https://kde.org/products/kirigami/), and Kscreenlocker adds a property to track past prompts. [KWin](https://userbase.kde.org/KWin) sees numerous improvements: relaxed nightlight constraints, simplified [Wayland](https://wayland.freedesktop.org/) popup handling, better input method windows, and enhanced screencast plugins. Plasma Mobile enhancements improve home screen interactions, translation issues, and swipe detection. Plasma Networkmanager and Plasma Workspace benefit from shared QQmlEngine and various bug fixes, including avatar image decoding and pointer warping on Wayland. * [Frameworks 6.4.0](https://kde.org/announcements/frameworks/6/6.4.0/): [Attica](https://api.kde.org/frameworks/attica/html/index.html) updates its gitignore to include VS Code directories. [Baloo](https://community.kde.org/Baloo) reverts a QCoreApplication change and ports QML modules. Breeze Icons introduces a ColorScheme-Accent and fixes data-warning icons. KArchive now rejects tar files with negative sizes and fixes crashes with malformed files. KAuth and KBookmarks add VS Code directories to gitignore. KCalendarCore adds missing QtCore dependencies and QML bindings for calendar models. KIO improves systemd process handling and deprecates unused features. [Kirigami](https://kde.org/products/kirigami/) enhances navigation and dialog components. KTextEditor adds a tool for testing JavaScript scripts and ensures even indent sizes, fixing multiple bugs. * [KDE Gear 24.05.2](https://kde.org/announcements/gear/24.05.2/): [Akonadi-calendar](https://api.kde.org/kdepim/akonadi-calendar/html/index.html) adds missing change notifications. [Dolphin](https://apps.kde.org/dolphin/) updates Meta-Object Compiler generation. [Filelight](https://apps.kde.org/filelight/) enables appx building and ensures hicolor icon presence while [Itinerary](https://apps.kde.org/itinerary/) fixes calendar permissions, corrupted notes, and the package introduces new extractors. [Kdenlive](https://kdenlive.org/en/) addresses timeline, aspect ratio, and compilation issues. [Okular](https://okular.kde.org/) fixes a crash with certain PDF actions. * [Supermin](https://github.com/libguestfs/supermin) 5.3.4: This update introduces several key enhancements, including support for OCaml 5 and kylinsecos. It improves package management by detecting [dnf5](https://github.com/rpm-software-management/dnf5) and omitting missing options. The update also refines OCaml compilation by using `-output-complete-exe` instead of `-custom` that fixes kernel filtering for the aarch64 architecture, and enables kernel uncompression on RISC-V. The update removes previously applied patches now included in the new tarball, helping to streamline the codebase and improve maintainability. * [Checkpolicy 3.7](https://github.com/SELinuxProject/selinux/releases/tag/3.7): The latest update brings support for Classless Inter-Domain Routing notation in nodecon statements, enhancing SELinux policy definition capabilities. Error messages are now more descriptive, and error handling has been improved. Key bug fixes include handling unprintable tokens, avoiding garbage value assignments, freeing temporary bounds types and performing contiguous checks in host byte order. ### Key Package Updates ### * [NetworkManager](https://networkmanager.dev/) 1.48.4: This update introduces support for matching Open vSwitch (OVS) system interfaces by MAC address, enhancing network interface management. Additionally, NetworkManager now considers the contents of `/etc/hosts` when determining the system hostname from reverse DNS lookups of configured interface addresses, improving hostname resolution accuracy. Subpackages updated include NetworkManager-bluetooth, NetworkManager-lang, NetworkManager-tui, NetworkManager-wwan, libnm0, and typelib-1\_0-NM-1\_0. These enhancements contribute to more robust and precise network configuration handling in Linux environments. * [libguestfs](https://libguestfs.org/) 1.53.5: This update includes significant enhancements and fixes. The `--chown` parameter is now correctly split on the ':' character, and a new checksum command is supported. Detection for Circle Linux and support for the LoongArch architecture have been added, including file architecture translation fixes. The update allows nbd+unix:// URIs and reimplements GPT partition functions using `sfdisk`. DHCP configuration improvements and a new `virt-customize --inject-blnsvr` operation enhance usability. Deprecated features include the removal of gluster, sheepdog, and tftp drive support. New APIs such as `findfs_partuuid` and `findfs_partlabel` improve functionality, while inspection tools now resolve PARTUUID and PARTLABEL in `/etc/fstab`. These updates enhance compatibility, performance, and functionality across various environments. * [glib2](https://wiki.gnome.org/Projects/GLib) 2.80.4: The latest update backports key patches: mapping `EADDRNOTAVAIL` to `G_IO_ERROR_CONNECTION_REFUSED`, handling files larger than 4GB in `g_file_load_contents()`, and correcting GIR install locations and build race conditions. Additionally, improvements in `gthreadedresolver` ensure returned records are properly reference-counted in `lookup_records()`. * [ruby3.3](https://www.ruby-lang.org/en/) 3.3.4: This release addresses a regression where dependencies were missing in the gemspec for some bundled gems such as net-pop, net-ftp, net-imap, and prime. Other fixes include preventing `Warning.warn` calls for disabled warnings, correcting memory allocation sizes in `String.new(:capacity)` and resolving string corruption issues. * [libgcrypt](https://gnupg.org/software/libgcrypt/index.html) 1.11.0: The latest update introduces several new interfaces and performance enhancements. New features include an API for Key Encapsulation Mechanism (KEM), support for algorithms like [Streamlined NTRU Prime](https://ntruprime.cr.yp.to/) sntrup761, Kyber, and Classic McEliece, and various Key Derivation Functions (KDFs) including HKDF and X963KDF. Performance improvements feature optimized implementations for SM3, SM4, and other cryptographic operations on ARMv8/AArch64, PowerPC, and AVX2/AVX512 architectures. Other changes include various enhancements for constant time operations and deprecates the `GCRYCTL_ENABLE_M_GUARD` control code. ### Bug Fixes ### * [orc](https://gstreamer.freedesktop.org/modules/orc.html) 0.4.39: * [CVE-2024-40897](https://www.suse.com/security/cve/CVE-2024-40897.html) was solved with versions before 0.4.39, which had a buffer overflow vulnerability in `orcparse.c`. * [java-21-openjdk](https://openjdk.org/projects/jdk/21/) 21.0.4.0: * [CVE-2024-21131](https://www.suse.com/security/cve/CVE-2024-21131.html) was a difficult-to-exploit vulnerability allowing unauthorized data modifications. * [CVE-2024-21138](https://www.suse.com/security/cve/CVE-2024-21138.html) was a vulnerability causing partial denial of service. * [CVE-2024-21140](https://www.suse.com/security/cve/CVE-2024-21140.html) was a vulnerability allowing unauthorized data access and modification; * [CVE-2024-21145](https://www.suse.com/security/cve/CVE-2024-21145.html) was similar. * [CVE-2024-21147](https://www.suse.com/security/cve/CVE-2024-21147.html) was the same, but for more critical data. * [ovmf](https://github.com/tianocore/tianocore.github.io/wiki/OVMF) 202402 had three months of CVE patches in its quarterly update. * [Mozilla Firefox](https://www.mozilla.org) 128.0: This release fixes 16 CVEs. The most severe was [CVE-2024-6604](https://www.mozilla.org/en-US/security/advisories/mfsa2024-29/#CVE-2024-6604); this was a memory safety bug in Firefox 128, Firefox ESR 115.13, Thunderbird 128 and Thunderbird 115.13. These bugs showed evidence of memory corruption that potentially allowed arbitrary code execution. * [ghostscript](https://www.ghostscript.com/index.html) 10.03.1) * [CVE-2024-33869](https://www.suse.com/security/cve/CVE-2024-33869.html) allowed bypassing restrictions via crafted PostScript documents. * [CVE-2023-52722](https://www.suse.com/security/cve/CVE-2023-52722.html) * [CVE-2024-33870](https://www.suse.com/security/cve/CVE-2024-33870.html) allows access to arbitrary files via crafted PostScript documents. * [CVE-2024-33871](https://www.suse.com/security/cve/CVE-2024-33871.html) allowed arbitrary code execution via crafted PostScript documents using custom Driver libraries in `contrib/opvp/gdevopvp.c`. * [CVE-2024-29510](https://www.suse.com/security/cve/CVE-2024-29510.html) allowed memory corruption and SAFER sandbox bypass via format string injection in a uniprint device. * [xwayland](https://wayland.freedesktop.org/) 24.1.1 3: * [CVE-2024-31080](https://www.suse.com/security/cve/CVE-2024-31080.html) had a vulnerability that could allow attackers to trigger the X server to read and transmit heap memory values, leading to a crash. * [CVE-2024-31081](https://www.suse.com/security/cve/CVE-2024-31081.html) could cause memory leakage and segmentation faults, leading to a crash. * [CVE-2024-31083](https://www.suse.com/security/cve/CVE-2024-31083.html) allowed arbitrary code execution by authenticated attackers through specially crafted requests. * [libreoffice](https://www.libreoffice.org/) 24.2.5.2: * [CVE-2024-5261](https://www.suse.com/security/cve/CVE-2024-5261.html) allows fetching remote resources without proper security checks. * [GTK3](https://www.gtk.org/) 3.24.43: * [CVE-2024-6655](https://www.suse.com/security/cve/CVE-2024-6655.html) allowed a library injection into a GTK application from the current working directory under certain conditions. * [netpbm](https://netpbm.sourceforge.net/) 11.7.0: * [CVE-2024-38526](https://www.suse.com/security/cve/CVE-2024-38526.html): doc, which provides API documentation for Python projects, had a vulnerability where pdoc --math linked to malicious JavaScript files from polyfill.io. ### Conclusion ### The month of July 2024 was marked by significant updates, security fixes and enhancements. The Linux Kernel 6.9.9 update introduced several key fixes and improvements across various subsystems, enhancing overall stability and performance. KDE Plasma 6.1.3 brought numerous UI improvements and better handling of Flatpak rebases. The updates to Frameworks 6.4.0 and KDE Gear 24.05.2 provided additional enhancements and bug fixes, improving user experience and system reliability. Critical security vulnerabilities were addressed in various packages, including Firefox, ghostscript, and xwayland, ensuring Tumbleweed remains secure, efficient, and feature-rich for all users. Additionally, the Aeon team announced the release of [Aeon Desktop to Release Candidate 3 status](https://www.reddit.com/r/AeonDesktop/comments/1edi3tr/aeon_rc3_released/) that came from the release of a [Tumbleweed snapshot](https://news.opensuse.org/2024/07/28/rc-image-released/) last week. For those Tumbleweed users who want to contribute or want to engage with detailed technological discussions, subscribe to the [openSUSE Factory mailing list ](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). The openSUSE team encourages users to continue participating through bug reports, feature suggestions and discussions. ### Contributing to openSUSE Tumbleweed ### Your contributions and feedback make openSUSE Tumbleweed better with every update. Whether reporting bugs, suggesting features, or participating in community discussions, your involvement is highly valued. ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) (Image made with DALL-E)
 news.opensuse.org
news.opensuse.org
An experimental "Pre-RC3" image for the [Aeon Desktop](https://aeondesktop.org) has been published and testers are encouraged to try out the final prototype before it becomes the official Release Candidate 3 (RC3). The new image can be downloaded from the [openSUSE development repository](https://download.opensuse.org/repositories/devel:/microos:/aeon:/images/devel_aeon/Aeon-Installer.x86_64.raw.xz). This prototype, which has been submitted to [openSUSE Factory](https://en.opensuse.org/Portal:Factory), introduces some significant changes and improvements. Notably, the `dd` backend in the tik installer has been replaced with a new `systemd-repart` backend. This change allows for the installation of Aeon with [Full Disk Encryption](https://en.opensuse.org/index.php?title=Portal:Aeon/Encryption) that enhances the security features of the operating system. Existing users of Aeon RC2 and earlier versions will need to perform a reinstall to take advantage of the new features destined for RC3. Due to the fundamental changes in partition layout necessary for the new encryption features, an in-place upgrade from RC2 is not feasible without risking data integrity, according to a post on the new [Aeon Desktop subreddit](https://www.reddit.com/r/AeonDesktop/). Users can utilize Aeon's [reinstall feature](https://en.opensuse.org/Portal:Aeon/InstallGuide#Backup_Existing_Users), which facilitates the backup and restoration of user data as long as a sufficiently large USB stick is used. Users installing the prototype image may encounter some packages from the OBS devel project. These can be removed by running `transactional-update --interactive dup` and selecting solutions that replace devel:microos packages with official ones. Testers are encouraged to provide feedback and report any issues encountered during the testing phase on the [Aeon Desktop bug report page](https://bugzilla.opensuse.org/enter_bug.cgi?product=openSUSE+Aeon&format=guided). Next Steps ---------- If the prototype is accepted into Factory and becomes RC3, the development of Aeon will be in its final stages before an official release. RC3 will serve as the basis for writing openQA tests for Aeon, which are crucial for ensuring the desktop's stability and functionality. There is a possibility of an RC4, which aims to streamline the installer process by embedding the full Aeon install within the installer image, potentially reducing the download size by 50 percent. If this approach is not feasible in the short term, it may be revisited post-release. [Full Disk Encryption](https://en.opensuse.org/index.php?title=Portal:Aeon/Encryption) is set up in one of two modes: Default or Fallback. Get more info about that in the [Aeon Desktop Introduces Comprehensive Full Disk Encryption](https://news.opensuse.org/2024/07/12/aeon-desktop-intros-fde/) article. ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
 news.opensuse.org
news.opensuse.org
[Full Disk Encryption](https://en.wikipedia.org/wiki/Disk_encryption) is planned to be introduced in the forthcoming release candidate of the [Aeon Desktop](https://aeondesktop.org) to enhance data security for its users. The feature is expected to be included in the upcoming Release Candidate 3 (RC3). [Full Disk Encryption](https://en.opensuse.org/index.php?title=Portal:Aeon/Encryption) is designed to protect data in cases of device loss, theft or unauthorized booting into an alternative operating system. Depending on the hardware configuration of a system, Aeon's encryption will be set up in one of two modes: Default or Fallback. ### Default Mode ### The Default Mode is the preferred method of encryption provided the system has the required hardware. This mode utilizes the [Trusted Platform Module](https://en.wikipedia.org/wiki/Trusted_Platform_Module)(TPM) 2.0 chipset with `PolicyAuthorizeNV` support (TPM 2.0 version 1.38 or newer). In this mode, Aeon Desktop measures several aspects of the system's integrity. These including: * [UEFI Firmware](https://en.wikipedia.org/wiki/UEFI) * [Secure Boot](https://en.wikipedia.org/wiki/UEFI#Secure_Boot) state (enabled or disabled) * Partition Table * Boot loader and drivers * Kernel and `initrd` (including kernel command line parameters) These measurements are stored in the system's TPM. During startup, the current state is compared with the stored measurements. If these match, the system boots normally. If discrepancies are found, users are prompted to enter a Recovery Key provided during installation. This safeguard ensures that unauthorized changes or tampering attempts are flagged. ### Fallback Mode ### The Fallback Mode is employed when the necessary hardware for Default Mode is not detected. This mode requires users to enter a passphrase each time the system starts. While it does not check system integrity as comprehensively as Default Mode, [Secure Boot](https://en.wikipedia.org/wiki/UEFI#Secure_Boot) is strongly recommended to ensure some level of security, confirming that the bootloader and kernel have not been tampered with. Contrary to initial concerns, Default Mode is not less secure than Fallback Mode despite not requiring a passphrase at startup. The strong integrity checks in Default Mode protect against attacks that could bypass normal authentication methods. For example, it can detect changes to the kernel command line that could otherwise allow unauthorized access. Furthermore, it safeguards against modifications to `initrd` thereby preventing potential passphrase capture in Fallback Mode. [Secure Boot](https://en.wikipedia.org/wiki/UEFI#Secure_Boot), while optional in Default Mode due to the comprehensive integrity checks, is critical in Fallback Mode to maintain system security. Disabling [Secure Boot](https://en.wikipedia.org/wiki/UEFI#Secure_Boot) in Fallback Mode increases vulnerability to tampering and attacks aimed at capturing the passphrase. Aeon's implementation of Full Disk Encryption provides robust security options tailored to the capabilities of users' hardware. By offering both Default and Fallback modes, Aeon ensures that all users can benefit from enhanced data protection. The inclusion of this feature in RC3 marks a significant step forward in safeguarding user data against potential threats. Aeon users are encouraged to read and bookmark the [Aeon Encryption Guide](https://en.opensuse.org/index.php?title=Portal:Aeon/Encryption). ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) (Image made with DALL-E)
 news.opensuse.org
news.opensuse.org
Welcome to the monthly update for openSUSE Tumbleweed for June 2024. This month was busy with events like the [Community Summit in Berlin](https://events.opensuse.org/conferences/CSBerlin) and the [openSUSE Conference](https://events.opensuse.org/conferences/oSC24), but a number of snapshots continued to roll out to users. Developers, system administrators and users receive updates designed to enhance your experience and ensure high levels of security and performance. Should readers desire a more frequent amount of information about snapshot updates, readers are encouraged to subscribe to the [openSUSE Factory mailing list](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). Let’s go! ### New Features and Enhancements ### * [Linux Kernel](https://www.kernel.org/) 6.9.7: This kernel introduces several important fixes and enhancements across various subsystems. Key updates include addressing undefined references in netfilter when `CONFIG_SYSCTL` is disabled, correcting [TCP](https://en.wikipedia.org/wiki/Transmission_Control_Protocol) Fast Open handling, and resolving a conflicting quirk in [Advanced Linux Sound Architecture](https://en.wikipedia.org/wiki/Advanced_Linux_Sound_Architecture) for Realtek devices. Improvements in file system writeback operations, multi-threaded path handling and memory management for [Hisilicon](https://www.hisilicon.com) crypto drivers enhance stability. Networking updates include fixes for race conditions in [netpoll](https://github.com/cloudwego/netpoll), enhancements for specific SFP modules, and improvements in WiFi drivers such as RTW89, Ath9k, Ath12k, and MT76. Additional platform-specific updates address issues in ACPI, ARM64 configurations, HID device handling, and Bluetooth driver fixes. * [PipeWire](https://pipewire.org/) 1.2.0 and [WirePlumber](https://github.com/PipeWire/wireplumber) 0.5.4: PipeWire 1.2.0 introduces asynchronous processing, node.sync-group for synchronized scheduling, and improved config parsing error reporting. It also adds mandatory metadata support for buffer parameters, multiple data-loops with CPU affinity, and dynamic log level adjustments. Key fixes include RTP-SAP module enhancements, ROC 0.3 support, and improved Bluetooth BAP broadcast code parsing. WirePlumber 0.5.4 refines the role-based linking policy, allowing role-based sinks alongside standard audio operations and enabling regular filters to act as best targets. It addresses startup crashes due to empty config files, improves Bluetooth profile auto-switching, and fixes issues with DSP filters and infinite loop scenarios in autoswitching scripts. Together, these updates enhance the flexibility, reliability, and overall performance of audio management in Linux environments. Both also received updates in snapshot [20240627](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/thread/NX4WPXDCZIOL4SIPB3XQ45BENOXZYMDY/) * [Mesa](https://www.mesa3d.org/) and [Mesa-drivers](https://www.mesa3d.org/) 24.1.2: Both packages underwent a specfile cleanup, involving the relocation of Rust crate sources into subprojects folders and updates to `baselibs.conf`. Due to the maintenance burden associated with Rust crates as system dependencies, these crates are now downloaded as vendored dependencies, as detailed in the README-suse-maintenance.md. The update adds support for building libvulkan\_nouveau, including necessary Rust crates such as paste-1.0.14, proc-macro2-1.0.70, quote-1.0.33, syn-2.0.39, and unicode-ident-1.0.12. However, building libvulkan\_nouveau on [Leap](http://get.opensuse.org/leap/) is not possible due to the requirement for rust-cbindgen \>= 0.25. For more details, refer to the release notes at [https://docs.mesa3d.org/relnotes/24.1.2](https://docs.mesa3d.org/relnotes/24.1.2). * [KDE Plasma](https://kde.org/announcements/changelogs/plasma/6/6.1.0-6.1.1/) 6.1.1: [Discover](https://invent.kde.org/plasma/discover) improves UI elements and Packagekit support, while Dr Konqi corrects the Sentry dbus interface usage. Plasma Addons addresses reference issues in Effects/cube, and krdp ensures version compatibility and resolves session controller bugs. Kscreenlocker improves greeter functionality, and KWin introduces multiple fixes for shaders, tiling, and input panels. Libkscreen and libplasma update protocol versions and fix plugin loading issues. Plasma Desktop enhances task icon sizing, panel opacity and file dragging across screens. Plasma Audio Volume Control removes unnecessary symlinks, and Plasma Systemmonitor correctly positions loading overlays. Powerdevil improves battery protection UI and limits backlighthelper calls. * [Python-setuptools](https://pypi.org/project/setuptools/) 70.0: Key features in this new major version include emitting warnings for ignored [tools.setuptools] entries in `pyproject.toml`, improved error messaging for `pkg_resources.EntryPoint.require` and handling `None` location distributions more gracefully. The update also refreshes unpinned vendored dependencies, supports PEP 625 by standardizing package name and version in filenames and ensures encoding consistency for `.pth` files. Obsolete Python \< 3.8 code has been removed, and `pkg_resources` now uses `stdlib` `importlib.machinery`. Bug fixes address race conditions in the install command, improve handling of nested namespaces with `package_dir` and correct various `pkg_resources` method behaviors. The patch for reproducibility has also been refreshed. * [Xen](https://xenproject.org/) 4.18.2\_06: This version resolves intermittent system hangs when Power Control Mode is set to Minimum Power. Patches also improve CPU mask handling and interrupt movement in various scenarios. Upstream bug fixes include improvements in scheduler resource data management and include fixes for building with [GNU Compiler Collection](https://gcc.gnu.org/) 14. ### Key Package Updates ### * [NetworkManager](https://networkmanager.dev/) 1.48.2: This package updates support for matching OVS system interfaces by MAC address and fixes port reactivation and VPN secrets handling for 2-factor authentication. It saves connection timestamps during shutdown for proper autoactivation after restart. Key changes in 1.48.0 deprecate autotools building, add support for changing [OpenSSL](https://www.openssl.org/) ciphers for 802.1X authentication, and set unmanaged device reasons in the `StateReason` property visible in nmcli. Additionally, it replaces the `mac-address-blacklist` property with `mac-address-denylist`, improves WiFi 6 GHz band detection and optimizes performance to avoid high CPU usage during route updates. Previous version 1.46 adds brought dynamic SSID-based stable IDs, randomized MAC addresses and several enhancements for handling IPv6, D-Bus and cloud setup. * [ibus-table](https://mike-fabian.github.io/ibus-table/) 1.17.6: This update drops Python2 support, transitioning all scripts to [Python3](https://www.python.org/) using pyupgrade. It now allows the use of keys with Unicode keysyms in keybindings, enhancing customization and flexibility. Additionally, the `frames_per_buffer=chunk_size` option is now utilized in `self._paudio.open()` for improved audio handling. The update also includes translation enhancements from [Weblate](https://weblate.org/), with Czech translations reaching 36.6 percent, Japanese at 45.3 percent, and Chinese (Simplified) at 92.0 percent. * [btrfsprogs](https://btrfs.wiki.kernel.org/) 6.9: The `mkfs` utility now halts if the mount status cannot be determined when using the `--force` option and corrects the minimum size calculation for zoned devices. The check command removes the `--clear-ino-cache` option, shifting its functionality to the `rescue` command group, and adds detection and repair for incorrect file extent item `ram_bytes` values. The qgroup commands now sync the filesystem before searching for stale entries, handle uncleaned subvolumes and `squota` enabled scenarios, and display the cleaning status of subvolumes. The `receive` command fixes stream parsing for strict alignment hosts, and `tune change-csum` and `dump-tree` commands include updates for handling `dev-replace` status items. The `convert` command improves extent iteration for preallocated/unwritten extents. The build process now ensures compatibility with e2fsprogs 1.47.1 and improves header file dependency tracking. Documentation was also updated. * GNU’s [Emacs](https://www.gnu.org/software/emacs/) 29.4: An emergency bugfix took place in this release. In this update, arbitrary shell commands are no longer executed when enabling Org mode, significantly enhancing security by preventing the execution of potentially malicious commands. ### Bug Fixes ### * Python-dnspython 2.6.1: * [CVE-2023-29483](https://www.suse.com/security/cve/CVE-2023-29483.html) - Eventlet before 0.35.2 in dnspython allows remote "TuDoor" DNS attack interference. * [php8](https://www.php.net/) 8.3.8: * [CVE-2012-1823](https://www.suse.com/security/cve/CVE-2012-1823.html) involved a vulnerability where attackers could inject arguments into PHP-CGI, leading to potential security issues. The new vulnerability, [CVE-2024-4577](https://www.suse.com/security/cve/CVE-2024-4577.html), was discovered to bypass this original fix, allowing the same or similar types of argument injection attacks. The update ensures that this bypass is no longer possible, reinforcing the security measures originally put in place for CVE-2012-1823. * Similarly, the bypass of [CVE-2024-1874](https://www.suse.com/security/cve/CVE-2024-1874.html) was made with the fix to [CVE-2024-5585](https://www.suse.com/security/cve/CVE-2024-5585.html). * kernel-firmware-nvidia-gspx-G06 (NVIDIA GPU driver) * [CVE-2024-0090](https://www.suse.com/security/cve/CVE-2024-0090.html) was a vulnerability where a user can cause an out-of-bounds write. * [CVE-2024-0091](https://www.suse.com/security/cve/CVE-2024-0091.html) was a vulnerability where a user can cause an untrusted pointer dereference. A successful exploit of this vulnerability might lead to denial of service. * [CVE-2024-0092](https://www.suse.com/security/cve/CVE-2024-0092.html) was an improper check or improper handling of exception conditions might lead to denial of service. * XZ 5.6.2: * [CVE-2024-3094](https://www.suse.com/security/cve/CVE-2024-3094.html) Through a series of complex obfuscations, the liblzma build process extracts a prebuilt object file from a disguised test file existing in the source code, which is then used to modify specific functions in the liblzma code. This results in a modified liblzma library that can be used by any software linked against this library, intercepting and modifying the data interaction with this library. More details in snapshot [20240605](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/thread/3UNI5PRCGMBHLATQTHC5WRXK3D5HDNGK/) * cJSON v1.7.17: * [CVE-2024-31755](https://www.suse.com/security/cve/CVE-2024-31755.html) - A segmentation violation, which can trigger through the second parameter. ### Conclusion ### The month of June 2024 saw a range of significant updates, security fixes and enhancements. The Linux Kernel 6.9.7 update improved stability and performance. Mesa and Mesa-drivers 24.1.2 introduced Rust crate dependencies and improved Vulkan support. KDE Plasma 6.1.1 brought UI improvements and a major version of Python-setuptools 70.0 arrived for rolling release users. A few critical security vulnerabilities were taken care of and fixes related to the [XZ backdoor](https://news.opensuse.org/2024/04/12/learn-from-the-xz-backdoor/) continued, so that Tumbleweed remains secure, efficient and feature-rich for all users. For those Tumbleweed users who want to contribute or want to engage with detailed technological discussions, subscribe to the [openSUSE Factory mailing list ](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). The openSUSE team encourages users to continue participating through bug reports, feature suggestions and discussions. ### Contributing to openSUSE Tumbleweed ### Your contributions and feedback make openSUSE Tumbleweed better with every update. Whether reporting bugs, suggesting features, or participating in community discussions, your involvement is highly valued. ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) (Image made with DALL-E)
 news.opensuse.org
news.opensuse.org
[Slowroll](https://en.opensuse.org/openSUSE:Slowroll), which has a more modest update cadence than [Tumbleweed](https://get.opensuse.org/tumbleweed/), is gaining acceptance as a balance between the rapid updates of Tumbleweed's rolling releases and the traditional [Leap](https://get.opensuse.org/tumbleweed/) release. Slowroll is nearly ready for full deployment and the development team has been working diligently to prepare the next version bump, with planned updates scheduled for July 9, August 9 and Sept. 9. These updates are expected to maintain a consistent monthly cadence to ensure users have timely and stable updates. One of the critical updates pulled in will include the latest [OpenSSH](https://github.com/openssh/openssh-portable) CVE fixes, which have already been made available in Tumbleweed. This fix enhances the security of Slowroll & ensure that it remains a robust and reliable distribution for users. ### Highlighted Features of Slowroll ### Balanced Update Cadence: Slowroll offers a monthly rolling update cycle that provides users with the latest features and security updates while ensuring stability through extensive testing and validation. Beta Phase: Slowroll is now in the Beta phase, indicating its near readiness for full deployment. Users can expect a reliable experience with continuous improvements. Continuous Improvement: The distribution integrates big updates approximately every month, alongside continuous bug fixes and security patches, ensuring a secure and up-to-date system. ### Statistics and Status ### According to the latest statistics available on the [Slowroll Stats page](http://stage3.opensuse.org:17080/munin/opensuse.org/stage3.opensuse.org/slowrollstats.html): * Tumbleweed had 2813 updated packages since the last version bump * Slowroll received 1316 updates from 871 different packages and only 339 updated rpms are Slowroll-specific builds ### Origins and Purpose ### Slowroll, introduced in 2023, was designed as an experimental distribution. Its primary goal is to offer a slower rolling release compared to Tumbleweed, thus enhancing stability without compromising on access to new features. The distribution continuously evolves with big updates integrated approximately every month, supported by regular bug fixes and security updates. It's crucial to understand that Slowroll is not intended to replace Leap. Instead, it provides an alternative for users who desire more up-to-date software at a slower pace than Tumbleweed but faster than Leap. If you try Slowroll, have a lot of fun - rolling... slowly! ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) (Image made with DALL-E)
 news.opensuse.org
news.opensuse.org
A new major version of Leap Micro is now available! Leap Micro 6.0 images can be found at [get.opensuse.org](https://get.opensuse.org/leapmicro/6.0/). Leap Micro 6.0 uses a brand-new codebase, comes with plenty of new appliances and, for the first time, enters images for public cloud. About Leap Micro ---------- Leap Micro 6.0 is a rebranded [SUSE Linux Enterprise Micro 6.0](https://www.suse.com/products/micro/) which is an ultra-reliable container and Virtual Machine host by SUSE. Leap Micro is released twice a year and has support over two releases. Leap Micro 5.4 is now EOL ---------- With the release of [Leap Micro 6.0](https://get.opensuse.org/leapmicro/6.0/), [Leap Micro 5.4](https://news.opensuse.org/2023/04/27/leap-micro-54-leap-155-enters-rc/) reaches End Of Life; users will no longer receive maintenance updates and are advised to upgrade. More conservative users can stay on Leap Micro 5.5, which will receive updates until the release of Leap Micro 6.1. Understanding Image variants ---------- All of Leap and SLE Micro generally come in two variants either Base or Default. Both Base and Default have a container stack, but only the Default variant has the Virtual Machine stack. If you do not plan to use VMs and you care for space, then the Base might be a variant just for you. All of our images offered at [get-o-o](https://get.opensuse.org/leapmicro/6.0/) are the Default ones (VMs+containers) as we expect they're suitable for most users. All appliances including Base variants (without virtualization stack) can be downloaded directly from [https://download.opensuse.org/distribution/leap-micro/6.0/appliances/](https://download.opensuse.org/distribution/leap-micro/6.0/appliances/) Explaining individual appliances ---------- A general recommendation for everyone use is the [self-install image](https://www.youtube.com/watch?v=j8kWT7HSjbw). It's a bootable image with a quick wizard that writes the preconfigured image to your drive and grows the root partition. This process from boot takes about 5 minutes. The preconfigured image is a raw bootable image you can manually write/dd to the disk or SD card. Images can be configured via Ignition/Combustion or will default to the jeos-firsboot wizard. We have a Real-time image with kernel-rt, qcow image for KVM, VMWare image, and a brand new raw image with [Full Disk Encryption](https://www.youtube.com/watch?v=Zd0kLDQsz88). Users who want to try our FDE image within a VM will need to make sure that they're using emulated tpm-2 chip and UEFI. This can be achieved easily with virt-manager. SLE Micro 6.0 dropped the traditional installer in favor of self-install media, therefore Leap Micro 6.0 doesn't have it either. The new Packages image is not a bootable media. This is just an image with an offline repository in case you need it. Leap Micro 6.0 comes for the first time also with [Public Cloud Images](https://build.opensuse.org/project/show/Cloud:Images:LeapMicro_6.0). Images will soon be available with all major public cloud providers. Upgrading from 5.X ---------- A recommendation is to make a clean install since this is a brand-new major version. For those who'd like to try migration, please follow the [upgrade guide](https://en.opensuse.org/SDB:System_upgrade_to_LeapMicro_6.0). Release Notes ---------- Users can refer to [SLE Micro 6.0 Release notes](https://www.suse.com/releasenotes/x86_64/SL-Micro/6.0/index.html). Leap Micro 6.0 uses [openSUSE-repos](https://github.com/openSUSE/openSUSE-repos) for repository management. It is highly recommended to pay attention to this detail, especially for those who migrate. Here is an [article explaining how openSUSE repos work](https://news.opensuse.org/2023/07/31/try-out-cdn-with-opensuse-repos/). Leap Micro 6.0 has no longer a [dedicated SLE update repo](https://github.com/openSUSE/openSUSE-repos/blob/main/opensuse-leap-micro5-repoindex.xml). This has been merged into the [main repository](https://github.com/openSUSE/openSUSE-repos/blob/main/opensuse-leap-micro6-repoindex.xml). ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
 news.opensuse.org
news.opensuse.org
[Leap 15.6](https://news.opensuse.org/2024/06/12/leap-unveils-choices-for-users/) install media were refreshed to address an issue with old secure boot signing key for [ppc64le](https://bugzilla.suse.com/show_bug.cgi?id=1226272#c7) and [s390x](https://bugzilla.suse.com/show_bug.cgi?id=1226215). Refreshed images from Leap 15.6 [Build 710.3](https://openqa.opensuse.org/tests/overview?distri=opensuse&version=15.6&build=710.3&groupid=50) are already available for download at [get.opensuse.org](https://get.opensuse.org/leap/15.6/). So now you can enjoy installation with secure boot on more exotic architectures. Happy Hacking!
So I often have to install and test different programs. I do not want programs to access the Internet immediately. After a while I might want to allow it, so it should be easy to allow or disallow internet access at the application level. Basically I wonder if there is an easy way to do this. It seems that [OpenSnitch](https://github.com/evilsocket/opensnitch) can do this, but it doesn't seem to work on OpenSuse. I might be able to get it to work eventually, but before I spend hours tinkering with it, do you know of a better solution? Might this even be possible with the built-in firewall or AppArmor?
 news.opensuse.org
news.opensuse.org
openSUSE Leap Micro 6.0 Beta is now available! We expect that it will very quickly transition to RC and GA as the infra readiness advances. Leap Micro 6.0 Beta images can be found at [get.opensuse.org](https://get.opensuse.org/leapmicro/6.0/) or directly at [download.opensuse.org](https://download.opensuse.org/distribution/leap-micro/6.0/appliances/). About Leap Micro ---------- Leap Micro 6.0 is a rebranded [SUSE Linux Enterprise Micro 6.0](https://www.suse.com/products/micro/) which is an ultrareliable container and VM host by SUSE. This is the first publicly released product based on the fresh code base "SUSE Linux Framework One" (previously known as ALP). Leap Micro 6.X is available for x86\_64 and aarch64, released every 6 months, and supported until the next-next release is out. That means that Leap Micro 6.0 will become EOL once Leap Micro 6.2 gets released. All pieces related to [Rancher and Elemental](https://elemental.docs.rancher.com/) are purposely excluded from Leap Micro 6.X as SLE Micro for Rancher is free for use without any subscription within Rancher deployments. No more traditional installer ---------- Leap Micro 6.X is deployed via [self-install image](https://www.youtube.com/watch?v=j8kWT7HSjbw) which writes a preconfigured image to the disk and enlarges root partition. Users can use [combustion, ignition](https://documentation.suse.com/sle-micro/6.0/html/Micro-deployment-raw-images/index.html#deployment-preparing-configuration-device) or default to the jeos-firstboot wizard to do the initial setup of the system. Do not get mistaken by the availability of openSUSE-Leap-Micro-6.0-\*.iso is not installable. We refer to the image as a Packages image, which is basically an offline repository on a DVD. New FDE, VMWare, and Cloud images ---------- Aside from the self-install image Micro 6.0 comes with qcow, Full Disk Encryption, and RealTime images. All images can be found at [download.opensuse.org](https://download.opensuse.org/distribution/leap-micro/6.0/appliances/) For the first time Leap Micro 6.X has also cloud-init therefore shortly after the release we will also have [cloud images](https://build.opensuse.org/project/show/Cloud:Images:LeapMicro_6.0) available on GCP, Azure, and AWS. Changes to the product building ---------- Leap Micro 6.X is using the new [product composer](https://build.opensuse.org/package/show/openSUSE:Tools/product-composer) instead of the old product builder. This allowed us to consume update-info from the newly designed maintenance workflow of SLE Micro 6.0 and was preferred by the openSUSE maintenance team. Changes to the repositories and maintenance workflow ---------- Leap Micro 5.X users receive all updates released for relevant SLE Micro version via a repository named [repo-sle-update](https://github.com/openSUSE/openSUSE-repos/blob/main/opensuse-leap-micro5-repoindex.xml#L26). This particular repository no longer exists in Leap Micro 6.X. Instead, the [repo-main](https://github.com/openSUSE/openSUSE-repos/blob/main/opensuse-leap-micro6-repoindex.xml#L8) repository will contain all released updates for the relevant version of SUSE Linux Micro to date. Please note that the repository path slightly changed too, we'll ensure that migration via transactional-update shell followed by zypper dup --releaser 6.0 works via compatibility symlinks on download server. New way of managing repository definitions ---------- [openSUSE-repos](https://news.opensuse.org/2023/07/31/try-out-cdn-with-opensuse-repos/) is not new to our users, however, for the first time, openSUSE Leap Micro 6.0 deployments come with openSUSE-repos preinstalled. openSUSE repos uses a local [RIS](https://en.opensuse.org/openSUSE:Standards_Repository_Index_Service) service that easily lets us maintain repository definitions with a package update. Users migrating from 5.5/5.4 releases are advised to install `zypper in openSUSE-repos` to ensure they have up-to-date [repository paths](https://download.opensuse.org/distribution/leap-micro/6.0/product/repo/). Documentation ---------- Please refer to [SLE Micro 6.0 documentation](https://documentation.suse.com/sle-micro/6.0/) including Release notes. Reporting Issues ---------- Please refer to the Leap Micro section in our [Submitting bug reports page](https://en.opensuse.org/openSUSE:Submitting_bug_reports#Regular_release_products). Next steps ---------- Missing maintenance setup was a long-term blocker for the transition out from Alpha, otherwise, the distribution itself is stable and feature-full. Now that we have it, we need to polish some remaining infrastructure issues and users can expect a release within the next few days. Ideally before [oSC2024](https://events.opensuse.org/conferences/oSC24/) next week.
 news.opensuse.org
news.opensuse.org
NUREMBERG, Germany – The release of [Leap 15.6](https://get.opensuse.org/leap/15.6/) is official and paves the way for professionals and organizations to transition to SUSE's enterprise distribution with extended support or prepare for the next major release, which will be Leap 16. Demands for robust, secure and stable operating systems in the digital infrastructure sector are more critical than ever. The combination of the community-driven [Leap 15.6](https://get.opensuse.org/leap/15.6/) and [SUSE Linux Enterprise 15](https://www.suse.com/products/server/) Service Pack 6, which integrates new features and enhancements, offers an optimal solution for managing critical infrastructure. Notably, SUSE's general support and [extended support]]([https://www.suse.com/products/long-term-service-pack-support/](https://www.suse.com/products/long-term-service-pack-support/)) versions; these [Product Support Lifecycles](https://www.suse.com/lifecycle/) last well beyond Leap 15's lifespan, ensuring longer and reliable service for users. [SLE 15](https://www.suse.com/products/server/) SP 6 is a feature release, so users can expect several more features in the [Leap 15.6](https://get.opensuse.org/leap/15.6/) release. This alignment ensures businesses and professionals using Leap for operational needs can enjoy a clear, supported transition to an enterprise environment, which is crucial in a move for systems that require long-term stability and enhanced security. As organizations strategize their upgrade paths, adopting an enterprise-grade solution like SUSE becomes a strategic decision, especially for those managing extensive networks and critical data across various sectors. Since being released on May 25, 2018, Leap has added several additions like container technologies, immutable systems, virtualization, embedded development, along with other high-tech advances. A [rise in usage](https://metrics.opensuse.org/) from each minor release shows that entrepreneurs, hobbyists, professionals and developers are consistently choosing Leap as a preferred Linux distribution. [Leap 15.6](https://get.opensuse.org/leap/15.6/) is projected to receive maintenance and security updates until the end of 2025 to ensure sufficient overlap with the next release. This will provide users with plenty of time to upgrade to the release's successor, which is Leap 16, or switch to SUSE's extended service support version. Users interested in commercial support can use a [migration tool](https://en.opensuse.org/SDB:How_to_migrate_to_SLE) to move to SUSE's commercial support version. The inclusion of the [Cockpit](https://cockpit-project.org/)[1] package in openSUSE Leap 15.6 represents a significant enhancement in system and container management capabilities for users. This integration into Leap 15.6 improves usability and access as well as providing a link between advanced system administration and user-friendly operations from the web browser. The addition underscores openSUSE's commitment to providing powerful tools that cater to both professionals and hobbyists. Leap does not come with a SELinux policy, so SELinux capablities for Cockpit are not functioning. Container technologies receive a boost with Podman 4.8, which includes tailored support for Nextcloud through quadlets, alongside the latest releases of Distrobox, Docker, python-podman, Skopeo, containerd, libcontainers-common, ensuring a robust container management system. Virtualization technologies are also enhanced, featuring updates to Xen 4.18, KVM 8.2.2, libvirt 10.0, and virt-manager 4.1. The Leap 15.6 release incorporates several key software upgrades enhancing performance and security. It integrates Linux Kernel 6.4, which provides backports for some of latest hardware drivers, which offer performance enhancements. OpenSSL 3.1 becomes the new default and provides robust security features and updated cryptographic algorithms. Database management systems receive significant updates with MariaDB 10.11.6 and PostgreSQL 16. Redis 7.2 offers advanced data handling capabilities and the software stack is rounded out with PHP 8.2 and Node.js 20; both received updates for better performance and security in web development. Leap will also have OpenJDK 21 providing improvements for enhanced performance and security in Java-based applications. Updates in telecommunications software are seen with DPDK 22.11 and Open vSwitch versions 3.1 and OVN 23.03. The KDE environment advances with the introduction of KDE Plasma 5.27.11, which is the latest Long Term Support version, Qt 5.15.12+kde151, and KDE Frameworks 5.115.0, as well as Qt6 version 6.6.3, facilitating smooth application operations with updated Python bindings for PyQt5 and PyQt6 aligning with Python 3.11. Many unmaintained Python packages were removed as part of a transition to Python 3.11; more details can be found in the [release notes](https://doc.opensuse.org/release-notes/x86_64/openSUSE/Leap/15.6/index.html). GNOME 45 brings enhancements to the desktop environment, adding features that elevate the user experience. Audio technologies see major upgrades with the release of PulseAudio 17.0 and PipeWire 1.0.4, which improve hardware compatibility and Bluetooth functionality, including device battery level indicators. These updates collectively enhance the system’s stability and user experience and make Leap 15.6 a compelling choice for professionals, companies and organizations. Leap can be downloaded at get.opensuse.org. ### End of Life ### Leap 15.5 will have its End of Life (EOL) six months from today’s release. Users should update to Leap 15.6 within six months of today to continue to receive security and maintenance updates. ### Download Leap 15.6 ### To download the ISO image, visit [https://get.opensuse.org/leap/](https://get.opensuse.org/leap/) If you have a question about the release or found a bug, we would love to hear from you at: [https://t.me/openSUSE](https://t.me/openSUSE) [https://chat.opensuse.org](https://chat.opensuse.org) [https://lists.opensuse.org/opensuse-support/](https://lists.opensuse.org/opensuse-support/) [https://discordapp.com/invite/openSUSE](https://discordapp.com/invite/openSUSE) [https://www.facebook.com/groups/opensuseproject](https://www.facebook.com/groups/opensuseproject) ### Get involved ### The openSUSE Project is a worldwide community that promotes the use of Linux everywhere. It creates two of the world’s best Linux distributions, the Tumbleweed rolling-release, and Leap, the hybrid enterprise-community distribution. openSUSE is continuously working together in an open, transparent and friendly manner as part of the worldwide Free and Open Source Software community. The project is controlled by its community and relies on the contributions of individuals, working as testers, writers, translators, usability experts, artists and ambassadors or developers. The project embraces a wide variety of technology, people with different levels of expertise, speaking different languages and having different cultural backgrounds. Learn more about it on opensuse.org 1 [Root login is disabled by default. Please read details in the [Try Cockpit in Leap Release Candidate](https://news.opensuse.org/2024/04/29/try-cockpit-in-leap-rc/) article. \*\*\*\*\* Two bugs related to Chrome with Wayland on [GNOME 45](https://en.opensuse.org/openSUSE:Known_bugs_15.6#GNOME) may see a fix coming in an update. \*\*\*\*\* ### Retrospective ### Provide your feedback to our release team by visiting [survey.opensuse.org/](https://survey.opensuse.org/) and taking our [retrospective survey](https://survey.opensuse.org/). ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) \<sub\>\<sup\>(Image made with DALL-E)\</sup\>\</sub\>
 news.opensuse.org
news.opensuse.org
Members of [openSUSE Project](https://www.opensuse.org/) are excited about the launch of [Leap 15.6](https://get.opensuse.org/leap/15.6/) on June 12 and encourages people to host a Release Party. If you don’t know how to do this, there is a list of [steps below on how to have a successful release party](https://en.opensuse.org/openSUSE:Launch_party_HOWTO). If you’re interested in hosting your own Release Party, there’s a handy checklist to help you plan a successful event: * Find a Date: A weekend date is usually best, but flexibility is key. Find a common date that works for most people. * Find a Place: A café, bar, or Linux group meetup location works great. Whether you opt for a coffee and cake party or a beer and pizza gathering, the key is to have fun. * Cake: While not essential, a cake adds to the celebration. You can also bake openSUSE cookies. * Pictures: Capture the moment with photos or videos and share them on social media. Tag openSUSE on [X](https://x.com/openSUSE), [Facebook](https://www.facebook.com/en.openSUSE), [Mastodon](https://fosstodon.org/@opensuse), [BlueSky](https://bsky.app/profile/opensuse.bsky.social) or more. There is already a plan to have people to meet virtually in the [openSUSE Bar](https://meet.opensuse.org/bar) for the launch June 12. The virtual release party will feature members of the release team and community members. Join sometime on June 12 as participants from various countries are encouraged to join and interact with the openSUSE community. Some will celebration the event in Nuremberg. Certainly people at the [openSUSE Conference](https://events.opensuse.org/) will highlight the release during the [BBQ/Release Party](https://events.opensuse.org/conferences/oSC24/program/proposals/4697). These launch parties provide a chance for the community to connect with the people behind the project and to show an appreciation for contributors who make the release of Leap 15.6 possible. It's an excellent opportunity for the community to gather, celebrate and discuss the new release after months of development. Schedule your [release party](https://en.opensuse.org/openSUSE:Launch_parties) today on the wiki and have a lot of fun! ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world) (Image made with DALL-E)
 news.opensuse.org
news.opensuse.org
### What is openSUSE.Asia Summit? ### The openSUSE Project is excited to announce that [openSUSE.Asia Summit 2024](https://events.opensuse.org/conferences/oSAS24) will be held in Tokyo, Japan. The openSUSE.Asia Summit is an annual conference for users and contributors of openSUSE and FLOSS enthusiasts. The former summits received major participation from Indonesia, China, Taiwan, Japan, South Korea, and India. Since the first openSUSE.Asia Summit was held in Beijing in 2014, the summits have been great opportunities for the online community to gather in person, know each other, and share knowledge and experiences about openSUSE including applications running on it. However, COVID-19 made it difficult for 3 years. One of our goals of this year’s summit is to provide a place for communication. Please note that we will not accept talks by video call this year. ### The summit dates ### The summit will be held on Nov. 2 and 3. An excursion for speakers is expected on Nov. 4, which will be announced later. You might be interested in [Open Source Summit Japan](https://events.linuxfoundation.org/open-source-summit-japan/) and [Open Compliance Summit](https://events.linuxfoundation.org/open-compliance-summit/), held by the Linux Foundation near the venue just before our summit. ### Cross-Distro Track ### We are going to co-host the Cross-Distro Track by the collaboration with [Cross Distro Developers Camp](https://xddc.connpass.com) (XDDC). XDDC is a wider developer community of FLOSS OS distribution including openSUSE, Debian and Ubuntu and works together to resolve common issues especially related to Japanese. This year, we are considering inviting speakers and participants from other distribution communities, which will undoubtedly contribute to making the event even more exciting. Furthermore, it will be a great chance to let them know how openSUSE and its community are. ### Venue ###  The openSUSE.Asia Summit 2024 is going to be held in [SHIFT Inc.](https://en.shiftinc.jp/), located in Azabudai Hills, Minato-ku, Tokyo, Japan. SHIFT Inc. is a company that supports to create sellable products and services and to grow the business of its customers. It offers integrated IT solutions and consulting services, including development, testing, UI/UX, and security, with its outstanding knowledge in software quality assurance. * [SHIFT Inc.](https://en.shiftinc.jp/) [Azabudai Hills](https://www.azabudai-hills.com/en/) is a large-scale urban redevelopment project completed in November 2023. This area, which combines offices, residential units, retail outlets, and cultural facilities, is also a newly prominent tourist attraction. It is, of course, easy to access from Tokyo/Haneda airport and anywhere in the capital area by public transportation. ### Tokyo and Japan ###  Tokyo is the capital of Japan. Its infrastructure and global connectivity will help attendees travel to the summit. There are direct flights from major cities in Asia Pacific as well as Europe and North America to either Tokyo/Haneda or Tokyo/Narita. Tokyo is also a popular place for sightseeing with its unique culture, food, etc. Especially, characters from video games, anime, and comics, which are now common globally, attract tourists to Japan. In Tokyo, you can easily find character shops and get items related to works you love. * [Tokyo Manga and Anime Guide — japan-guide.com](https://www.japan-guide.com/e/e3052.html) * [Food & Drink in Tokyo ― GO TOKYO](https://www.gotokyo.org/en/see-and-do/drinking-and-dining/index.html) The number of tourists from abroad has recovered last year to the same level as before COVID-19. Due to the currency exchange rate, it will be a great chance to enjoy your trip to Japan while saving your money. However, if there is any possibility of attending the summit, you should book your hotel right away with a cancelable plan. Some of our recommended hotels start accepting reservations from 5 months ago, which is June 1. Because Nov. 4 is a public holiday in Japan, rooms in budget hotels become sold out soon, or you will need to pay for your hotel at an inappropriately expensive rate, which might not be covered by [the Travel Support Program](https://en.opensuse.org/openSUSE:Travel_Support_Program). Please also check the following web sites for tourism information in Tokyo and Japan: * [GO TOKYO (Tokyo Convention & Visitors Bureau) ](https://www.gotokyo.org/) * [Travel Japan (Japan National Tourism Organization) ](https://www.japan.travel/) * [Japan Guide](https://www.japan-guide.com/) ### Call for speakers ### We will start to call for speakers in June. Please read another post for the call for speakers on [news.opensuse.org](https://news.opensuse.org/), published in a couple of days. ### Wrapping Up ### The openSUSE.Asia Summit is a great opportunity for the openSUSE community to meet together. The attendees will be able to enjoy their stay in Tokyo during the summit. We are looking forward to seeing you this November in Tokyo. Have a lot of fun! ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
 news.opensuse.org
news.opensuse.org
Welcome to the monthly update for openSUSE Tumbleweed for May 2024. This month has seen a significant number of updates, enhancements, and crucial security fixes. Whether you are a developer, a system administrator, or a casual user, these updates are designed to enhance your experience and ensure the highest level of security and performance. Should readers desire a more frequent amount of information about snapshot updates, readers are encouraged to subscribe to the [openSUSE Factory mailing list](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). Let’s go! ### New Features and Enhancements ### * [Linux Kernel](https://www.kernel.org/) 6.9.1: The month of May had a couple updates for the Kernel, but so far remains at version 6.9.1, which addresses various issues and enhancing overall stability. The [mt76](https://openwrt.org/docs/techref/driver.wlan/mt76) driver for wifi saw improvements with the addition of missing chanctx operations for the mt7915 wifi card, enhancing functionality. A critical fix was made to the keys subsystem to prevent overwriting key expiration during instantiation, improving security. Support for system suspend/hibernation was enhanced for the Modem Host Interface subsystem with the addition of the `mhi_power_down_keep_dev()` [Application Programming Interfaces](https://en.wikipedia.org/wiki/API), which is beneficial for maintaining device states during power management operations. * [LLVM](https://llvm.org/) 18.1.6: Subpackages that were updated were clang-tools, clang18, libLLVM18, libclang-cpp18, libclang13, llvm18-gold. Fixed issues with generating incorrect thunks for functions with aligned parameters or incorrect return value passing when StructRet was used. `-Xclang` `-target-feature` `-Xclang +unaligned-scalar-mem` for enabling unaligned scalar memory accesses on CPUs without unaligned vector access support were introduced. Build failures when compiling AVX512 code with `-march=native` on machines without AVX512 were addressed. Crashes in the AArch64 backend related to `fcmp` instruction operands being true or false at the IR level were fixed and there was a fix to compiler crashes. * [KDE Frameworks](https://kde.org/announcements/frameworks/5/5.116.0/) 5.116.0: Breeze Icons received new icons for `audio/ogg` and `audio/x-vorbis+ogg` file types, as well as the `audio/vnd.wave` MIME type, enhancing support for audio file formats. Extra CMake Modules had notable updates including the dropping of attempts to set IMPORTED on targets with installed configurations in `ecm_add_qch`. KFileMetaData saw a fix with the handling of attribute namespacing and improved metadata accuracy and processing. KService addressed a warning related to the "mimeType `x-scheme-handler/file` not found" issue. * [udisks2](https://www.freedesktop.org/wiki/Software/udisks/) 2.10.1: This update features updated Ukrainian and German translations, improvements to testing for LVM2 RAID by wiping used devices, settling down before checking properties and rescanning vdevs after tests. Offline and online filesystem grow tests were added, and documentation for the Filesystem.Size property was clarified. A fix was implemented for Python class invocation in nvme tests, and a --no-partition-scan option was added for the loop-setup command in udisksctl. A `--no-partition-scan` option for the `loop-setup` command in udisksctl was added. * [firewalld](https://firewalld.org/) 2.1.2: The update to 2.1.2 includes several fixes: the policy now allows forwarding ports with the `to-addr` for `egress-zone=HOST`, the range check for large rule limits in rich rules has been corrected, and skip detection in the `fw-in-container` environment has been fixed during testing. * [snapper](https://github.com/openSUSE/snapper) 0.11.0: The update introduces asynchronous cleanup of stale [btrfs](https://btrfs.wiki.kernel.org) qgroups and reverts some parts to fix the build in the [Open Build Service](https://build.opensuse.org/). The cleanup service is now set to run every hour and qgroups are disabled if they do not exist to avoid failure when creating snapshots. Support for quarterly snapshots has been added, and a table-style selection is now based on codeset. * [GTK3](https://www.gtk.org/) 3.24.42: Printing is improved by avoiding access to freed printers. [Wayland](https://wayland.freedesktop.org/) fixes include correct monitor sizes, a crash related to tablet removal, inferred resizable edges for tiled windows, and ensuring commits occur soon after acknowledging a configure. [GTK4](https://www.gtk.org/) 4.14.4: A crash issue when there is no child was resolved and efficiency improvements were made in loading symbolic SVGs and handling color-free symbolics. Accessibility updates include making the gtk-demo sidebar search more accessible and stopping the emission of focus events. GDK introduced support for `XDG_ACTIVATION_TOKEN` and made defensive improvements for dmabuf. These improvements include handling unknown formats more carefully and using a narrower range for YUV formats. * [Mozilla Firefox](https://www.mozilla.org) 126.0. The browser brought had a major update and fixed 16 [Common Vulnerabilities and Exposures](https://en.wikipedia.org/wiki/Common_Vulnerabilities_and_Exposures). There was arbitrary JavaScript execution in PDF.js fixed with CVE-2024-4367. A potential permissions request bypass via clickjacking was fixed for CVE-2024-4764. There were memory safety bug fixes addressing CVE-2024-4778 and CVE-2024-4777; the latter helps with those for Firefox ESR 115.11 and Thunderbird 115.11. [sssd](https://sssd.io/) 2.9.5: The update introduces a new configuration option called `failover_primary_timeout`. This option allows users to configure how often SSSD tries to reconnect to a primary server after successfully connecting to a backup server. Previously, this interval was hardcoded to 31 seconds, which remains the default value. * [openldap2](https://www.openldap.org/) 2.6.7: The liblber library fixes a missing newline on long messages and libldap addresses exit handling issues with [OpenSSL3](https://www.openssl.org/), TLS usage with multiple LDAP URIs [OpenSSL](https://www.openssl.org/) cipher suite handling and handling of Diffie-Hellman parameter files with OpenSSL 3.0. The slapd service now honors the disclose option in matchedDN handling, improves regex testing in ACLs, and fixes sync replication with glued databases. * [iproute2](https://git.kernel.org/pub/scm/network/iproute2/iproute2.git) 6.9: The update introduces several new features and improvements: The `m_mirred` module now allows mirroring to block and the `tc` command adds `NLM_F_ECHO` support for actions and filters. The `ip` command has been enhanced with coupled\_control support for bonding and a new monitor command for [IOAM6](https://docs.kernel.org/networking/ioam6-sysctl.html). * [xwayland](https://wayland.freedesktop.org/) 24.1.0: The feature release addresses several regressions introduced in previous release candidate versions. The `eglstreams` support has been dropped. * [AppStream](https://www.freedesktop.org/wiki/Distributions/AppStream/) 1.0.3: Key features include enhanced validator checks to ensure description lists aren't translated, improved translation checks for descriptions and the ability to propagate selected custom entries to catalog output via the CLI compose command. Many other features were added. ### Key Package Updates ### * [tpm2-0-tss](https://github.com/tpm2-software/tpm2-tss) 4.1.0: This updated provided a major security fix for [CVE-2024-29040](https://www.suse.com/security/cve/CVE-2024-29040.html). Various bug fixes were implemented, including correcting the length check on FAPI auth callbacks, fixing the deviation from the CEL specification and resolving json syntax errors in FAPI profiles that were previously ignored by json-c. The update also adds support for new features and enables the usage of external keys for Fapi\_Encrypt. * [postgresql16](https://www.postgresql.org/) 16.3: A fix was made for [CVE-2024-4317](https://www.postgresql.org/support/security/CVE-2024-4317/), which could allow for an unprivileged database user to read most common values and other statistics from `CREATE STATISTICS` commands of other users. * Python 3.x versions had a fix for [CVE-2023-6597](https://www.suse.com/security/cve/CVE-2023-6597.html) A vulnerability was discovered in the [CPython](https://github.com/python/cpython). It affected versions 3.12.1, 3.11.7, 3.10.13, 3.9.18, 3.8.18, and earlier. This class would incorrectly follow symlinks during cleanup when there were permission errors. As a result, users with the ability to run privileged programs could potentially change the permissions of files pointed to by symlinks under certain conditions. ### Bug Fixes ### * [glib2](https://wiki.gnome.org/Projects/GLib) 2.80.2: * [CVE-2024-34397](https://www.suse.com/security/cve/CVE-2024-34397.html) - An issue in GNOME GLib allows spoofed D-Bus signals, affecting client behavior * [qt6-base](https://www.qt.io/product/qt6): * [CVE-2024-33861](https://www.suse.com/security/cve/CVE-2024-33861.html) - QStringConverter's invalid pointer callback can modify the stack, risking vulnerabilities in applications using QStringDecoder. * libxml2 2.12.7 * [CVE-2024-34459](https://www.suse.com/security/cve/CVE-2024-34459.html) - Buffer over-read in xmllint --htmlout can cause vulnerabilities in libxml2 before 2.12.7. * libarchive 3.7.4: * [CVE-2024-26256](https://www.suse.com/security/cve/CVE-2024-26256.html) - Remote Code Execution Vulnerability. * krb5 added some patches to fix memory leaks related to: * [CVE-2024-26458](https://www.suse.com/security/cve/CVE-2024-26458.html) * [CVE-2024-26461](https://www.suse.com/security/cve/CVE-2024-26461.html) * [CVE-2024-26462](https://www.suse.com/security/cve/CVE-2024-26462.html) * ovmf * [CVE-2022-36763](https://www.suse.com/security/cve/CVE-2022-36763.html) - `EDK2` vulnerability in `Tcg2MeasureGptTable()` allows heap buffer overflow via local network * python-Jinja2 3.1.4: * [CVE-2024-34064](https://www.suse.com/security/cve/CVE-2024-34064.html) - Jinja's `xmlattr` filter vulnerability allows non-attribute characters in keys, risking XSS attacks. * [tpm2-0-tss](https://github.com/tpm2-software/tpm2-tss) 4.1.0: * [CVE-2024-29040](https://www.suse.com/security/cve/CVE-2024-29040.html) is a flaw that allows an attacker to generate arbitrary quote data, which may not be detected by [Fapi\_VerifyQuote](https://tpm2-tss.readthedocs.io/en/stable/group___fapi___verify_quote.html). ### Conclusion ### The month of May 2024 had a steady flow of crucial security fixes, important updates, and notable enhancements across various packages for openSUSE Tumbleweed. The updates to the Linux Kernel, LLVM, KDE Frameworks and numerous other components ensure that Tumbleweed systems remain feature-rich and keep rolling. Developers and users alike benefit from the improvements, enhancements and new features. For those Tumbleweed users who want to contribute or want to engage with detailed technological discussions, subscribe to the [openSUSE Factory mailing list ](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). The openSUSE team encourages users to continue participating through bug reports, feature suggestions and discussions. ### Contributing to openSUSE Tumbleweed ### Your contributions and feedback make openSUSE Tumbleweed better with every update. Whether reporting bugs, suggesting features, or participating in community discussions, your involvement is highly valued. ### More Information about openSUSE: ### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
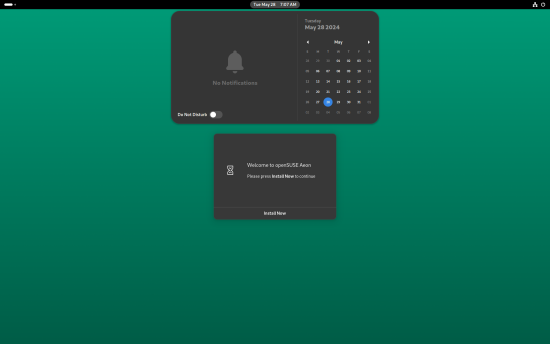 news.opensuse.org
news.opensuse.org
Looks like most of the improvements have nothing to do with GNOME, so they should also probably impact Kalpa (the KDE MicroOS distro). I'm particularly interested in these developments because I'm going to upgrade the CPU on my NAS (old Phenom II -> Ryzen 1700), and I'm considering reinstalling w/ MicroOS. It's currently running on an old SATA SSD, but NVMe drives are getting so cheap that it's probably worth an upgrade.
 news.opensuse.org
news.opensuse.org
The [openSUSE Project](https://get.opensuse.org/) has an official space on [Hugging Face](https://huggingface.co/openSUSE), which is a popular platform offering a range of open-source Artificial Intelligence models, tools and resources. The new namespace can be found at [huggingface.co/openSUSE](https://huggingface.co/openSUSE). Hugging Face is known for facilitating developers and researchers in working with advanced AI applications that include natural language processing (NLP) and computer vision. Having the openSUSE namespace provides community-driven development toward creating, sharing and improving AI models and datasets. One dataset has already been added. The first dataset is [openSUSE Cavil](https://github.com/openSUSE/cavil), which is a tool designed for license compliance, identification and legal reviews. By leveraging the rich AI models and datasets available through the Hugging Face platform, openSUSE Cavil can offer a more advanced and accurate detection of license issues and compliance. To get involved with the openSUSE Project on Hugging Face, individuals can sign up for an account. The registration process is straightforward and requires only basic information. Once registered, users can explore the openSUSE and view a collection of AI models and datasets created and shared by the community. Contributors are encouraged to share their AI models and datasets. Hugging Face offers tools and tutorials to assist with uploading and managing these contributions. Community members can work together on improving existing models or developing new ones. High-quality documentation and tutorials are vital for the success of the project. Community members can contribute by writing guides, creating video tutorials, or translating existing resources to broaden their accessibility. Users gain access to cutting-edge AI models and a collaborative environment where they can learn and expand their skills. Contributions to the project support the advancement of AI research and development within the open-source ecosystem. For more information and to participate, visit [huggingface.co/openSUSE](https://huggingface.co/openSUSE). #### More Information about openSUSE: #### **Official** * [openSUSE News](https://news.opensuse.org/) * [openSUSE Mailing List](https://lists.opensuse.org/archives/) * [openSUSE Wiki](https://en.opensuse.org/Main_Page) **Fediverse** * [https://discuss.tchncs.de/c/openSUSE@kbin.social](https://discuss.tchncs.de/c/openSUSE@kbin.social) * [https://discuss.tchncs.de/c/opensuse@lemmy.world](https://discuss.tchncs.de/c/opensuse@lemmy.world)
 news.opensuse.org
news.opensuse.org
[From the website](https://docs.openvino.ai/2024/home.html): > OpenVINO is an open-source toolkit for optimizing and deploying deep learning models from cloud to edge. It accelerates deep learning inference across various use cases, such as generative AI, video, audio, and language with models from popular frameworks like PyTorch, TensorFlow, ONNX, and more. Convert and optimize models, and deploy across a mix of Intel® hardware and environments, on-premises and on-device, in the browser or in the cloud.
 news.opensuse.org
news.opensuse.org
Important dates: - expected summit date is Nov. 2 and 3 soon after Open Source Summit Japan - call for speakers is going to end around the end of July There will be another announcement in a couple weeks.
 news.opensuse.org
news.opensuse.org
Welcome to the monthly update for openSUSE Tumbleweed for April 2024. This month began after addressing last month’s [supply chain attack against xz compression library](https://news.opensuse.org/2024/03/29/xz-backdoor/) for the rolling release. An [explanation of that XZ Backdoor, how it was address and what was learned](https://news.opensuse.org/2024/04/12/learn-from-the-xz-backdoor/) can be found on [news.opensuse.org](https://news.opensuse.org/2024/04/12/learn-from-the-xz-backdoor/). A flurry of updates, enhancements, and crucial security fixes arrived in openSUSE’s rolling release this month as the busy season for conferences begins. Should readers desire a more frequent amount of information about snapshot updates, readers are encouraged to subscribe to the [openSUSE Factory mailing list](https://lists.opensuse.org/archives/list/factory@lists.opensuse.org/). ### New Features and Enhancements * [Linux Kernel](https://www.kernel.org/): The month of April had a few kernel updates. Notable changes with the 6.8.5 version included mitigation for Branch History Injection (BHI) vulnerabilities, improvements to Spectre mitigation, updates for Intel graphics drivers, fixes for SMB client vulnerabilities and fixes for [RISC-V](https://riscv.org/) architecture. Version 6.8.7 included updates and fixes for [AMD](https://www.amd.com/en) display drivers, Intel i915 driver, x86 speculative execution vulnerabilities, [arm](https://www.arm.com/) 64 device tree files, DRM drivers, filesystem handling, and more. * [KDE Frameworks 6.1.0](https://kde.org/announcements/frameworks/6/6.1.0/): The `numpy` package introduces enhanced support for structured arrays and flexible indexing, while `pandas` incorporates improved handling of missing data and new methods for data manipulation. Additionally, the `matplotlib` package offers enhanced customization options for plot aesthetics. New algorithms for machine learning tasks in `scikit-learn` were included in the update. * [KDE Gear 24.02.2](https://kde.org/announcements/gear/24.02.2/): The KDE Gear 24.02.2 update encompasses a wide range of fixes and enhancements, including resolving issues with tag addition functionality in [Akonadi](https://api.kde.org/kdepim/akonadi/html/index.html), addressing translated shortcut and icon appearance problems in [Akregator](https://apps.kde.org/akregator/), various improvements and fixes in ark such as disabling RAR4 compression method, multiple fixes in [Elisa](https://apps.kde.org/elisa/) including volume slider and track playback issues and numerous enhancements in [Konsole](https://konsole.kde.org/). There were fixes for calendar selection and the todo view updates in [Korganizer](https://apps.kde.org/korganizer/). * [PHP8](https://www.php.net/) 8.3.6: There were significant bug fixes, security patches and improvements across different components including in the update. Besides fixes with Core, DOM, GD, Opcache and Session other fixes include: * FPM: Fixes have been applied to address issues with the configuration test running twice in daemonized mode and incorrect checks in `fpm_shm_free()`. * Gettext: Fixes have been made to address issues with `dcgettext` and `dcngettext` calls with specific configurations. * [MySQLnd](https://www.php.net/manual/en/book.mysqlnd.php): Various fixes have been applied, including correcting handshake response and charset length checks. * Random: Compatibility improvements have been introduced for PHP versions prior to 8.2, and issues with global `Mt19937` reset have been resolved. * Standard: Validation has been added for specific characters in the `mail()` function, and various bug fixes have been implemented, including addressing command injection and cookie bypass vulnerabilities. (Noted in [CVE-2024-1874](https://www.suse.com/security/cve/CVE-2024-1874.html), [CVE-2024-2756](https://www.suse.com/security/cve/CVE-2024-2756.html) and fixing issues with `mb_encode_mimeheader` and `password_verify` with [CVE-2024-3096](https://www.suse.com/security/cve/CVE-2024-3096.html) and [CVE-2024-2757](https://www.suse.com/security/cve/CVE-2024-2757.html). * [Mozilla Firefox](https://www.mozilla.org) 125.0.2. The browser brought new features such as: * Support for AV1 codec in Encrypted Media Extensions (EME) for improved video playback quality. * Enhanced PDF viewer capabilities with text highlighting. * Introduction of the URL Paste Suggestion feature, improving usability by allowing quick navigation to URLs copied to the clipboard. * Multiple critical security fixes addressing vulnerabilities like out-of-bounds reads and use-after-free errors that enhance browser security. * [dracut](https://dracut.wiki.kernel.org/index.php/Main_Page): There were improvements such as the addition of tpm2.target and systemd-tpm2-generator and several memory leak fixes. * [ffmpeg](https://www.ffmpeg.org/): Versions 4 and 6 took care of some video handling issues and made fixes for memory leaks with improved EOF handling. The updates addresses: * [CVE-2023-51793](https://www.suse.com/security/cve/CVE-2023-51793.html) and [CVE-2023-49502](https://www.suse.com/security/cve/CVE-2023-49502.html). * [CVE-2023-50008](https://www.suse.com/security/cve/CVE-2023-50008.html) and [CVE-2023-50007](https://www.suse.com/security/cve/CVE-2023-50007.html) * [sqlite3](https://www.sqlite.org/index.html): An update from version 3.45.2 to 3.45.3 addresses a long-standing bug affecting the accuracy of trigger responses in certain [UPSERT](https://www.sqlite.org/lang_upsert.html) operations to ensure for more reliable database operations. * [Flatpak](https://flatpak.org/): The 1.15.8 update had some security fixes to prevent sandbox escape and various other usability improvements. * [Python3.11](https://www.python.org/): The 3.11.9 version had various security patches and bug fixes, such as addressing [CVE-2023-52425](https://www.suse.com/security/cve/CVE-2023-52425.html), updating bundled [libexpat](https://libexpat.github.io/) to version 2.6.0, fixing possible crashes in `collections.deque.index()` and improves SSLContext behavior. * [Cppcheck](https://github.com/danmar/cppcheck): New checks in version 2.14.0 include: * eraseIteratorOutOfBounds: Warns about calling `erase()` on an iterator that is out of bounds, enhancing the robustness of code. * returnByReference: Warns when a large class member is returned by value from a getter function, which can impact performance and memory usage. ### Other Package Updates * [SDL2](https://github.com/libsdl-org/SDL): Version 2.30.2 introduces support for various new controllers, including the 6-button SEGA Mega Drive Control Pad and the Hori Fighting Stick EX2. * [Cryptsetup](https://gitlab.com/cryptsetup/cryptsetup): Version 2.7.2 addressed several issues, including fixes for OPAL device formatting and activation. * [SpamAssassin](https://spamassassin.apache.org/): A package with a great name, version 4.0.1 enhances URL shortener link redirection handling and improved TxRep locking management, which bolsters email security for users. ### Bug Fixes * [Xwayland](https://wayland.freedesktop.org/xserver.html): [CVE-2024-31083](https://www.suse.com/security/cve/CVE-2024-31083.html) This critical security vulnerability mitigates an Xorg servers vulnerable due to use-after-free flaw in `ProcRenderAddGlyphs()`, allowing authenticated attackers to execute arbitrary code. * [PHP8]((https://www.php.net/):[CVE-2023-51793](https://www.suse.com/security/cve/CVE-2023-51793.html), [CVE-2023-49502](https://www.suse.com/security/cve/CVE-2023-49502.html), [CVE-2023-50008](https://www.suse.com/security/cve/CVE-2023-50008.html) and [CVE-2023-50007](https://www.suse.com/security/cve/CVE-2023-50007.html) * [glibc](https://www.gnu.org/software/libc/): [CVE-2024-2961](https://www.suse.com/security/cve/CVE-2024-2961.html) allows buffer overflow when converting to ISO-2022-CN-EXT, causing crashes or variable overwrites. [libxml2](https://github.com/GNOME/libxml2): [CVE-2024-25062](https://www.suse.com/security/cve/CVE-2024-25062.html) was a vulnerablity to use-after-free via crafted XML documents. * [Python3.11](https://www.python.org/): [CVE-2023-52425](https://www.suse.com/security/cve/CVE-2023-52425.html), [CVE-2023-6597](https://www.suse.com/security/cve/CVE-2023-6597.html) * [QEMU](https://www.qemu.org/): Backports and bugfixes were made for a flaw that allows a malicious guest to crash QEMU and cause a denial of service condition with [CVE-2024-3567](https://www.suse.com/security/cve/CVE-2024-3567.html). [CVE-2024-3446](https://www.suse.com/security/cve/CVE-2024-3446.html) could affect arbitrary code execution and [CVE-2024-3447](https://www.suse.com/security/cve/CVE-2024-3447.html) was also backported. * [Freerdp2](https://www.freerdp.com/): Version 2.11.5 provided fixes for [CVE-2023-40574](https://www.suse.com/security/cve/CVE-2023-40574.html), which experienced an Out-Of-Bounds Write in the `writePixelBGRX` function that was likely due to incorrect variable calculations, and [CVE-2023-40575](https://www.suse.com/security/cve/CVE-2023-40575.html), which results in crashes. ### Conclusion The month of April 2024 had a blend of feature enhancements and crucial security fixes. From improved gaming support with SDL2 to strengthened encryption practices with Cryptsetup, users benefited from a host of updates aimed at enhancing functionality, stability and security. Other packages to update in Tumbleweed during the month were [Mesa](https://www.mesa3d.org/), [GTK4](https://www.gtk.org/), [transactional-update](https://github.com/openSUSE/transactional-update) and more . For those Tumbleweed users that want to contribute, subscribe to the openSUSE Factory mailing list. The openSUSE team encourages users to continue participating through bug reports, feature suggestions and discussions. ### Contributing to openSUSE Tumbleweed Your contributions and feedback make openSUSE Tumbleweed better with every update. Whether reporting bugs, suggesting features, or participating in community discussions, your involvement is highly valued.
 news.opensuse.org
news.opensuse.org
Looks like Leap 15.6 will ship with Cockpit, which looks pretty cool. I just set up a new VPS w/ Leap 15.5, so I'm thinking about giving this a try. I'm not a fan of YaST on the CLI, and I'm not going to install a GUI on my VPS, so being able to just SSH tunnel to the admin panel sounds _really_ nice. Has anyone tried Cockpit ([project link for the lazy](https://cockpit-project.org/))? It seems like it can manage most popular distros, so that's a pretty big value prop over YaST, which is pretty much only for SUSE. It looks like it's a RedHat project, but it's cool that openSUSE is pulling it in for 15.6.
Slowroll just bumped its Tumbleweed snapshot version a few hours ago. This update contains everything since the previous snapshot 2024-02-13, including the Plasma and Gnome updates.
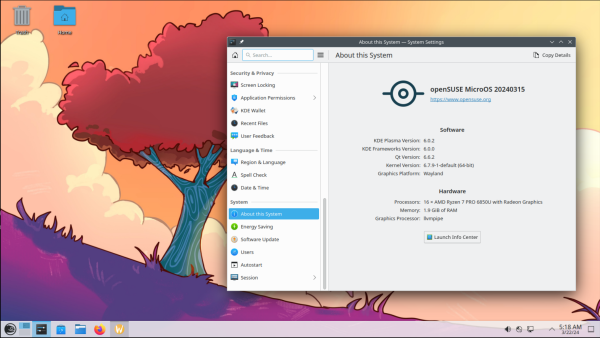 news.opensuse.org
news.opensuse.org
by Douglas DeMaio
So, I updated Tumbleweed, and the updates to KDE caused my Plasma/Wayland session to restart, breaking the updates part way through. I wasn't watching at the time so took some while to debug! Spent some time learning how to use nm-cli, because new half-upgraded KDE wouldn't load the network widget. It looks like something else may have changed and mucked up in the half-update (and of course I rebooted like a wise-man/dummy/i-dont-know-but-at-least-it-didnt-make-it-work) but iterations of trying things in nmcli eventually worked! Finally tried zypper dup again and saw the session restart, so finished the job from the virtual terminal! At last, I seem to have a working computer again, and I might just brave updating my main laptop. (I cancelled the update while it was still downloading packages, after seeing the breakage on the other laptop!)
Any idea when this will hit tumbleweed? I'm really looking forward to this release!
 news.opensuse.org
news.opensuse.org
It's a bit quiet here so for now I'll start linking the latest openSUSE news here.
Hey, I've gone ahead and decided to try out TW as my first foray into the Linux world, and I started by getting it set up on my laptop. Everything seems to be working pretty well for me (other than wifi passwords not saving by default, but I seem to have found a workaround that's not too inconvenient). I later tried to get it set up on my desktop and the experience was very sluggish and I was curious if there would be an obvious reason as to why. I understand that I'm giving few details here, but the sluggishness was not felt at all on my laptop and was felt immediately on my desktop. I have since installed fedora on my desktop and it's been very solid and noticeably not sluggish. I thought I should perhaps try to understand what potential issues occurred so I can get a better understanding of the system I'm using. Thanks in advance for any input.
From what i have read, the winning logos are not guaranteed to be chosen, so we will have to wait for an official announcement. I think there is a meeting today, so I would keep an eye on the official wiki and news pages. On the meeting on tuesday (12.12), the competition results have been discussed but I don't know what's been said. [Notes](https://etherpad.opensuse.org/p/weeklymeeting20231212) for the meeting on 12.12 [Notes](https://etherpad.opensuse.org/p/weeklymeeting20231214) for the meeting on 14.12
The deadline has passed, but I'm not sure if all entries have been added to the wiki yet.
 lists.opensuse.org
lists.opensuse.org
Slowroll repos have been moved to a new location. Upcoming version bump, to catch up with Tumbleweed, announced.
So, after Debian Stable disappointed me by crashing Wayland and Baloo on a fresh install with KDE, I decided to try out OpenSUSE Tumbleweed: - The installer is awesome. I've never seen such a great interface for choosing which packages to install before. - 8 seconds of Grub timeout seems a bit much. - The Desktop looks and feels like the "engineer's distro" it claims to be. The wallpaper, splash screen, login screen and theming look and feel beautiful and professional. - Printer and scanner setup was awful. YAST doesn't find my printer (which Debian did and set up printing and scanning automatically). The KDE printer setting fails to load, claiming it is "forbidden" even after prompting me for the root password. Googling the issue, I disable the built-in firewall, which changes nothing. At this point, I take drastic measures, uninstall YAST and the firewall so nothing can get in the way of the usual setup process. I download the drivers from the manufacturer and try manual settup with Cups, which also fails with a permission error. I try adding my user to the lpt and lpadmin groups, which does nothing. The documentation for setting up scanners only covers USB-attached devices, not those in a network. I find out that for automatic setup, I need cups-airprint and sane-airscan. The latter is only available through a user's home repo, which the docs specifically tell you not to do. I do it anyway, and the printer/scanner finally shows up configured correctly. - Web Video doesn't work out of the box. I follow the docs to activate the Packman repo and install the necessary codecs, despite the warning of a lemmy user that this broke their KDE desktop. I still don't know if it makes a difference whether I install all codecs from Packman or only those that aren't available in the main repo. There's nothing about it in the docs. - Package management is obviously not optimized for Tumbleweed, but for LEAP. Why is the YAST Update GUI installed by default if you are supposed to only use zypper? Why does zypper throw a warning every time I do zypper dup, even though that's the only way you're supposed to update? To get the packages I need for normal laptop use, I have to activate a couple of additional repos. The docs warn you that not all repos are compatible with each other, without going into detail. So I guess, there's a risk of instability, but I have no way of knowing how big it is. Also, I'm still not sure what zypper refresh does. dup seems to work without it, and zypper warns me when a repo is out of date, so it must have some way of checking that without refreshing. For now, I just do "zypper dup && zypper refresh" every time, like on Debian. I don't know if there's a good reason why some repos are set to auto-refresh "no" by default. The docs don't tell me. - For spotify, I tried out spotify-easyrpm, which builds an installable RPM from the official snap, and adds a systemd service for automatic updates. REALLY great idea and I was excited when I found what it does. Only it failed to install some needed dependencies, and after installing them manually, the Spotify client opened a black window. - On the other hand, I was impressed how much thought was put into packaging so your software is ready for use after installation. Installing flatpak pulls in a package that automatically enables the flathub repo, for example. And I love that updates come in "mini releases" that went through automated testing as a whole, instead of on a package-by-package basis. My summary: You can feel that this is a distro made by Germans. It's a lot more complex under the hood than for example Debian, with special tools built in where others rely on simple config files, and a lot of thought put into it. But also quite a few parts that feel overengineered, and an even stricter free software policy that Debian has nowadays. My main issue with it is lack of good documentation online. What is there is not all collected in one place, a bit spotty and sometimes contradictory. After setting it all up and learning about its quirks, I'll stick with it however. Despite its issues, it feels like a well-made distro, and the combination of a tested rolling release with easily accessible and granular user repos and its own build system are unique.
openSUSE
!opensuse@lemmy.worldopenSUSE is an open, free and secure operating system for PC, laptops, servers and ARM devices. Managing your emails, browsing the web, watching online streams, playing games, serving websites or doing office work never felt this empowering. And best part? It's not only backed by one of the leaders in open source industry, but also driven by lively community.